The latest cyber security resources, news and updates written by industry experts. Check out our blog packed full of resources to help secure your business from cyber attacks.
Read Content Written By Cyber Security Experts
-
Saudi Aramco $50 Million Data Breach Explained
In this week’s episode of The Breach Report, we cover the Saudi Aramco data breach. This breach is different from the spate of recent ransomware attacks in that it isn...
-
Recent Cyber Attacks & Data Breaches In 2021
As data breaches become more pervasive in our interconnected world so must our understanding of modern day cyber attacks. In this video series, we sit down with cyber securi...
-
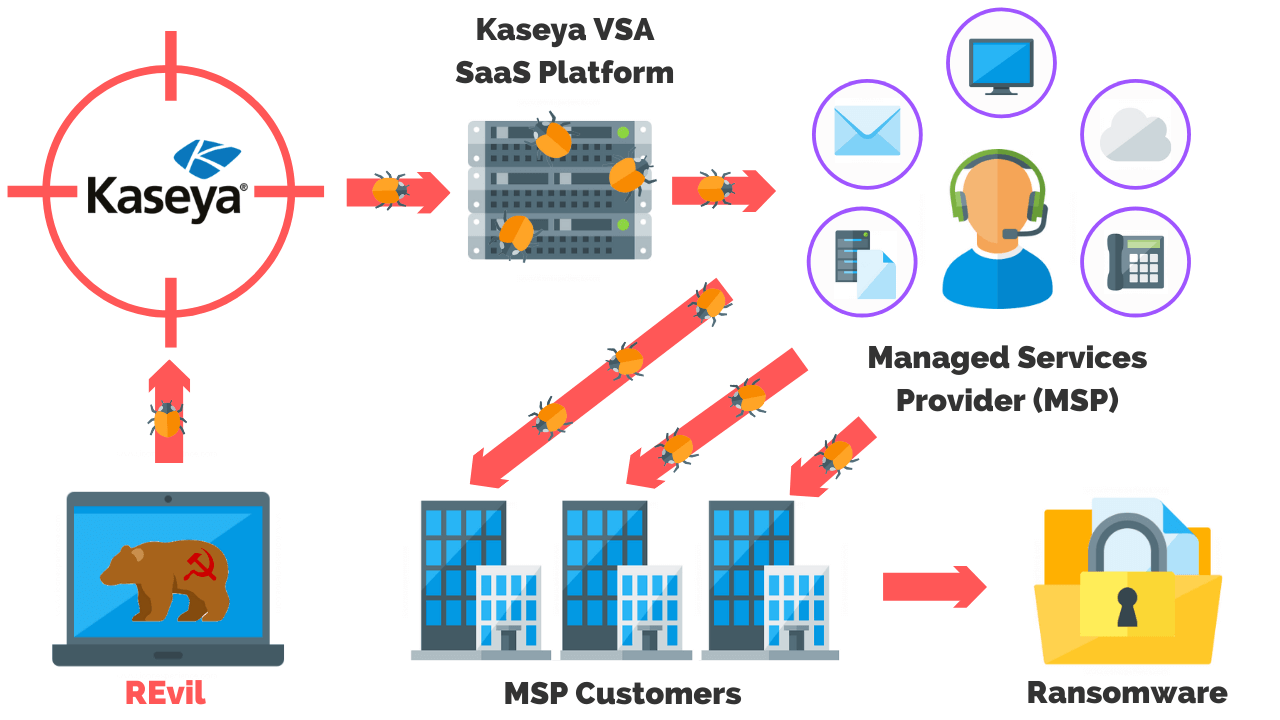
Kaseya VSA Ransomware Attack Explained
In this week’s episode of The Breach Report, we cover one of the largest ransomware attacks in history impacting up to 1500 companies. The breach we’re talking a...
-
2021 Cyber Security News, Analysis, & Updates
In this video series, we review the latest cyber security news, industry analysis, and updates on recent cyber attacks that have happened so far this year. Contents &...
-
Accellion Data Breach: What Happened & Who Was Impacted?
Accellion FTP Data Breach Explained The Accellion file transfer application (FTA) data breach has impacted over 100 companies, organizations, universities, and govern...
-
Pulse Secure VPN Breach: What Happened & What Are The Implications?
Pulse Secure VPN Zero-Day Vulnerability Explained The Pulse Secure VPN zero-day has been exploited resulting in the breach of several undisclosed defense firms and go...
-
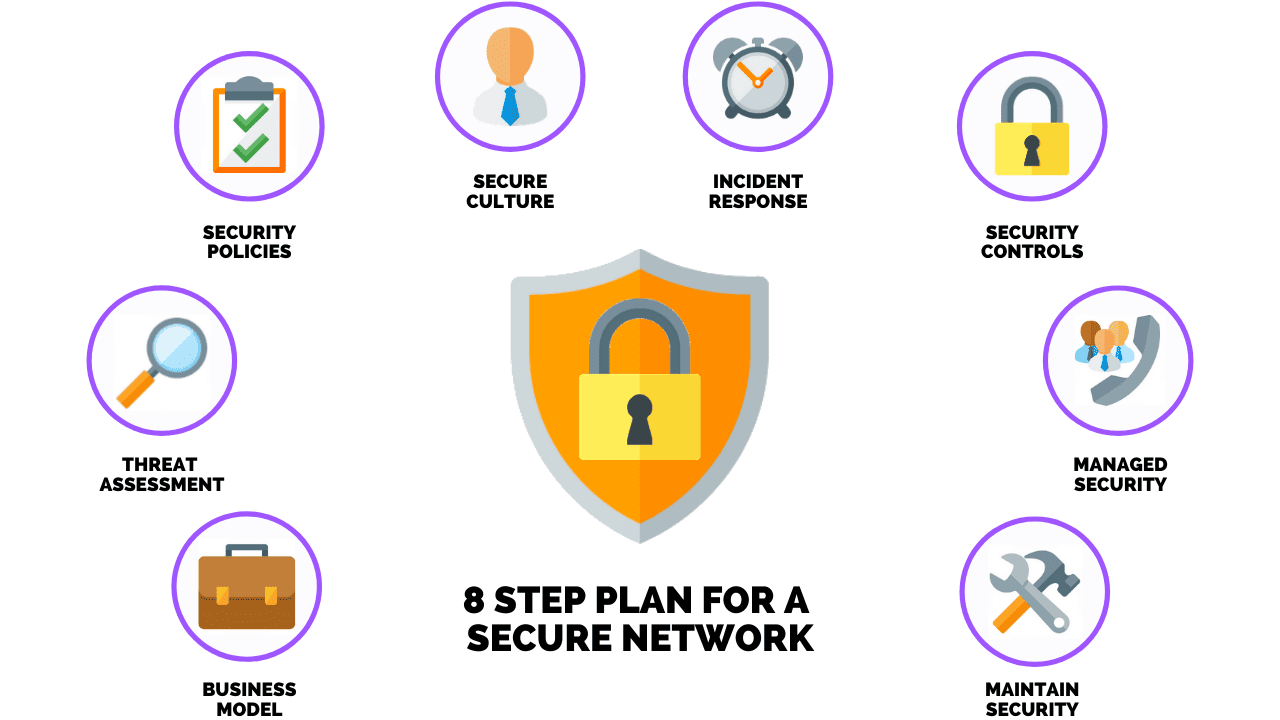
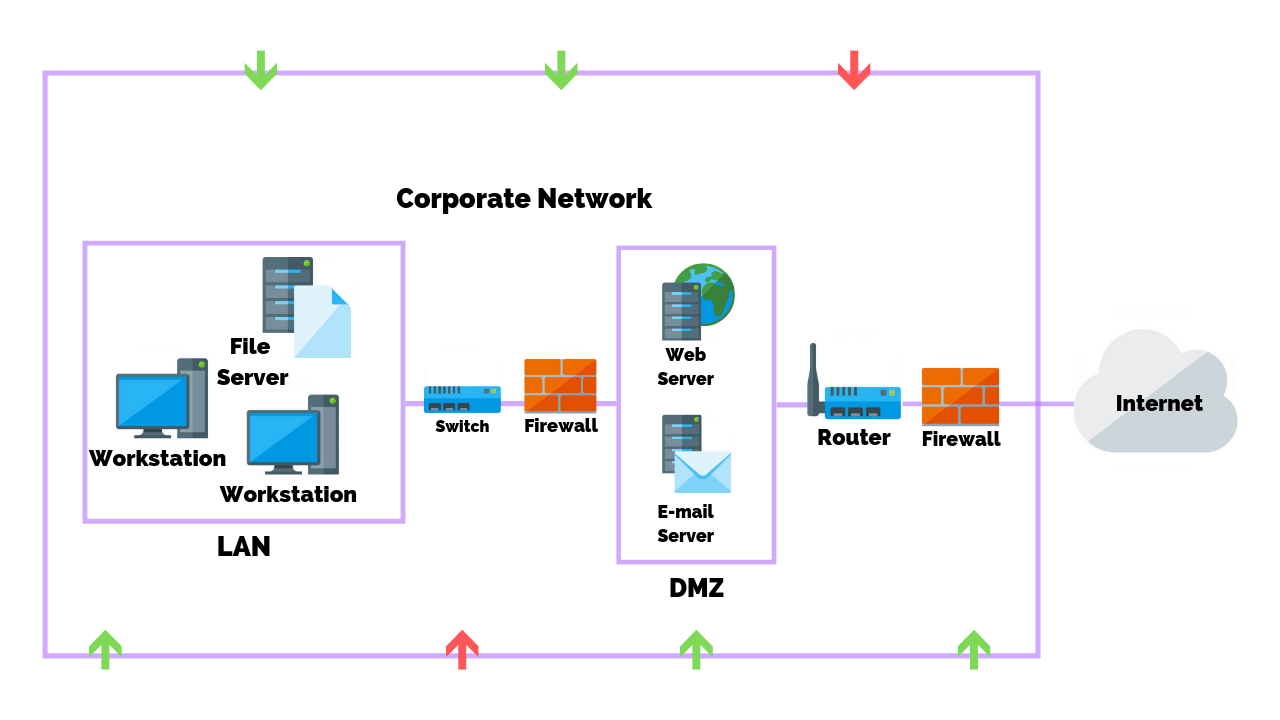
How To Develop & Implement A Network Security Plan
Protecting your business and its data from today’s threats and adversaries is a challenging endeavor requiring expertise and professionally managed resources. You also...
-
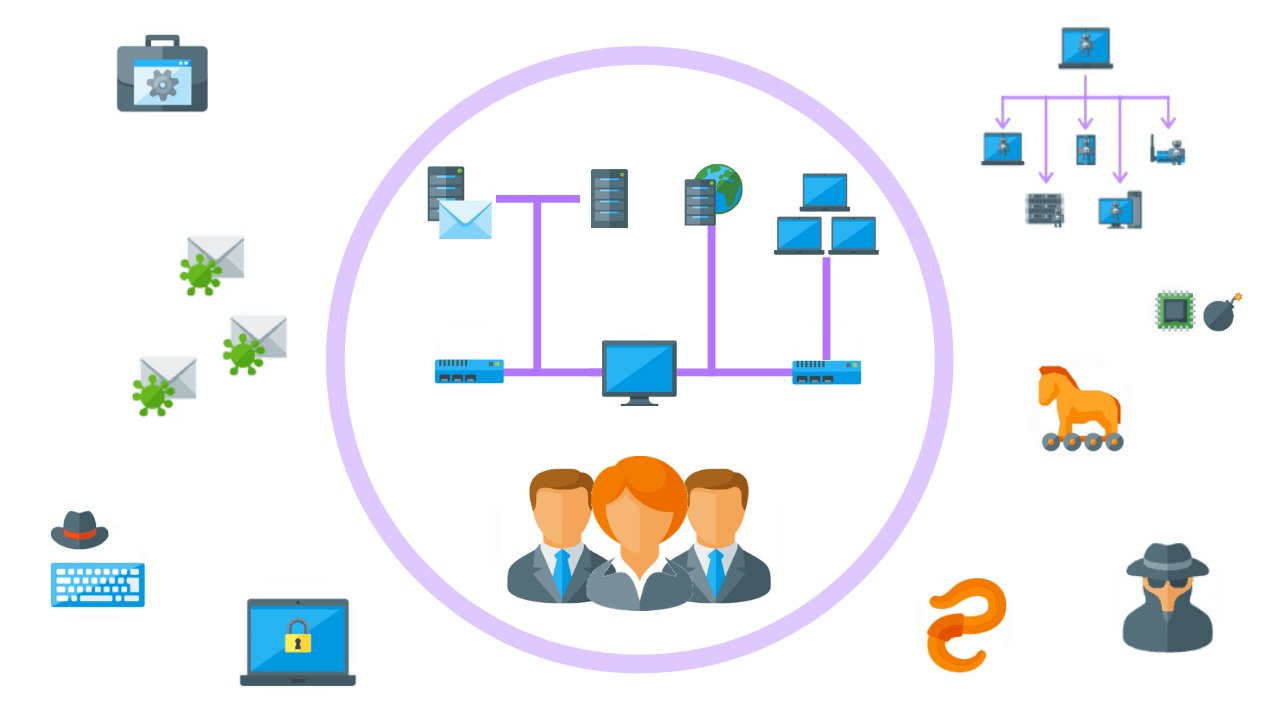
9 Common Types Of Malware (And How To Prevent Them)
The most common types of malware include viruses, keyloggers, worms, trojans, ransomware / crypto-malware, logic bombs, bots/botnets, adware & spyware, and rootkits. You can mi...
-
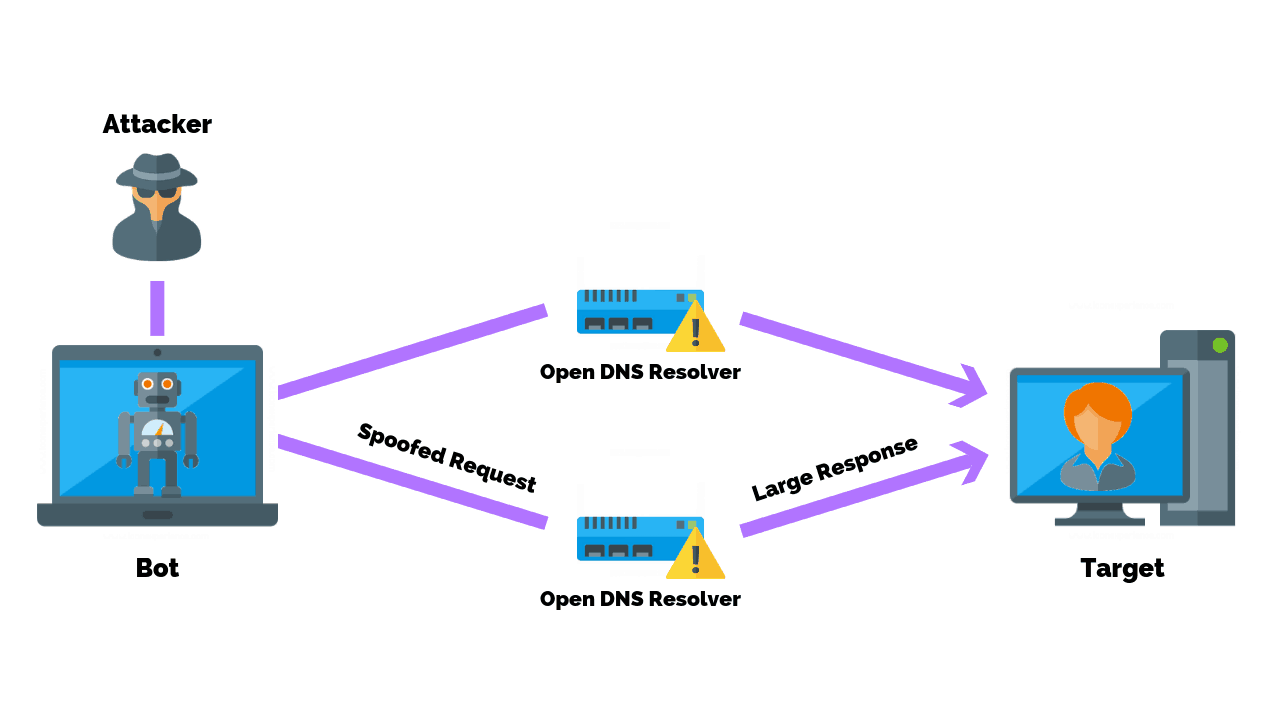
How To Prevent A Domain Name Server (DNS) Amplification attack
A domain name server amplification attack is a popular form of DDoS attack that attempts to flood a target system with DNS response traffic You can prevent a DNS amplificati...
-
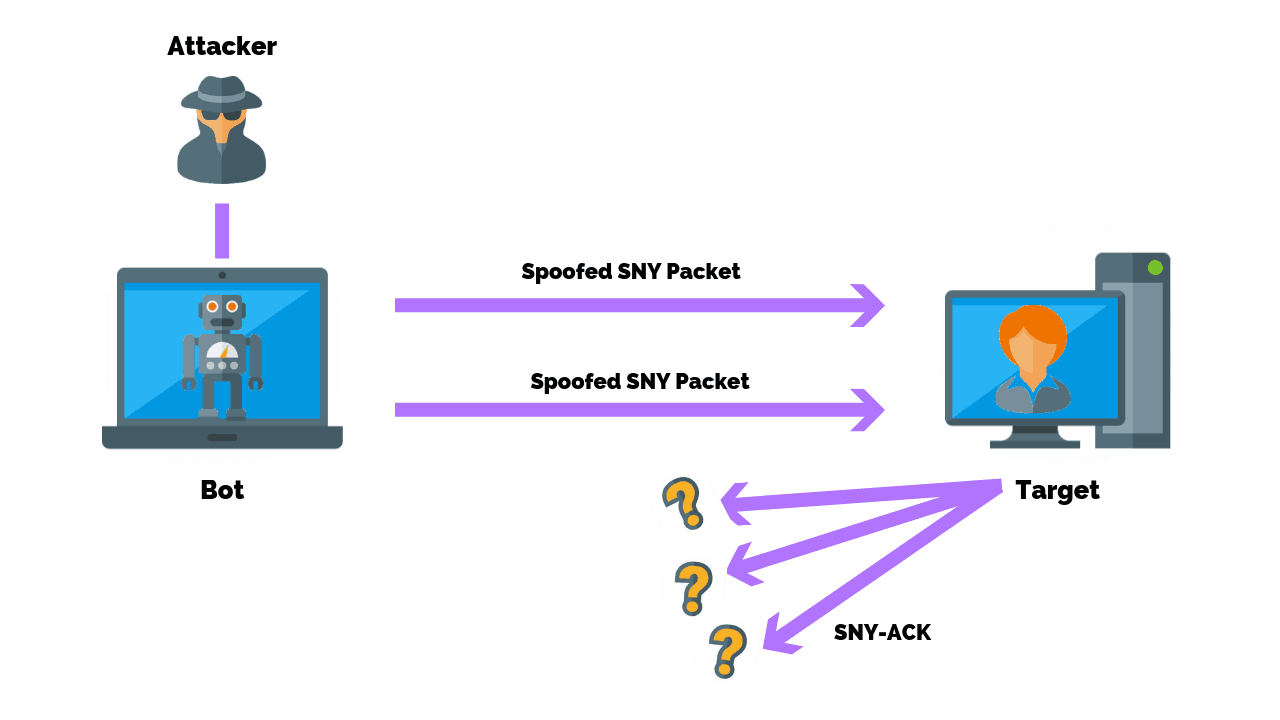
How To Prevent A SYN Flood Attack
SYN floods are a form of DDoS attack that attempts to flood a system with requests in order to consume resources and ultimately disable it. You can prevent SYN flood attacks...
-
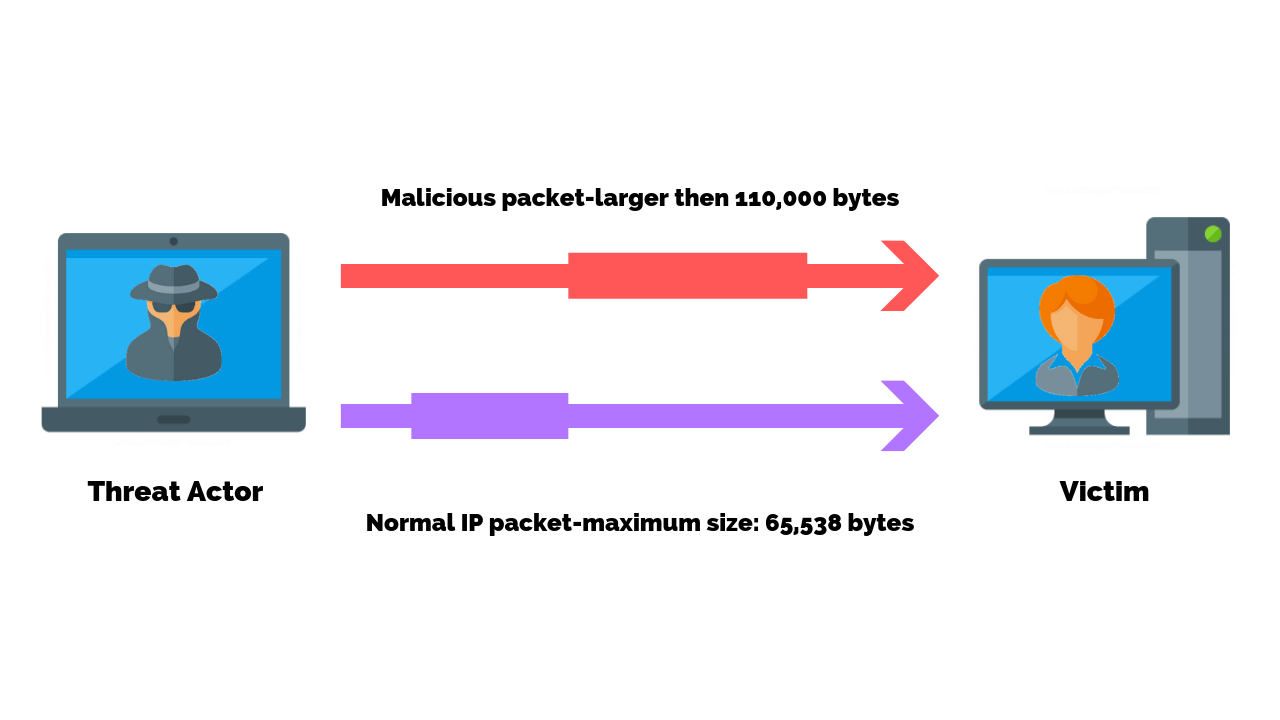
How To Prevent A ICMP Flood Attack
Ping attacks are a form of DDoS attack that attempts to flood a system with requests in an attempt to disable it. You can prevent ping attacks by configuring your firewall, ...
-
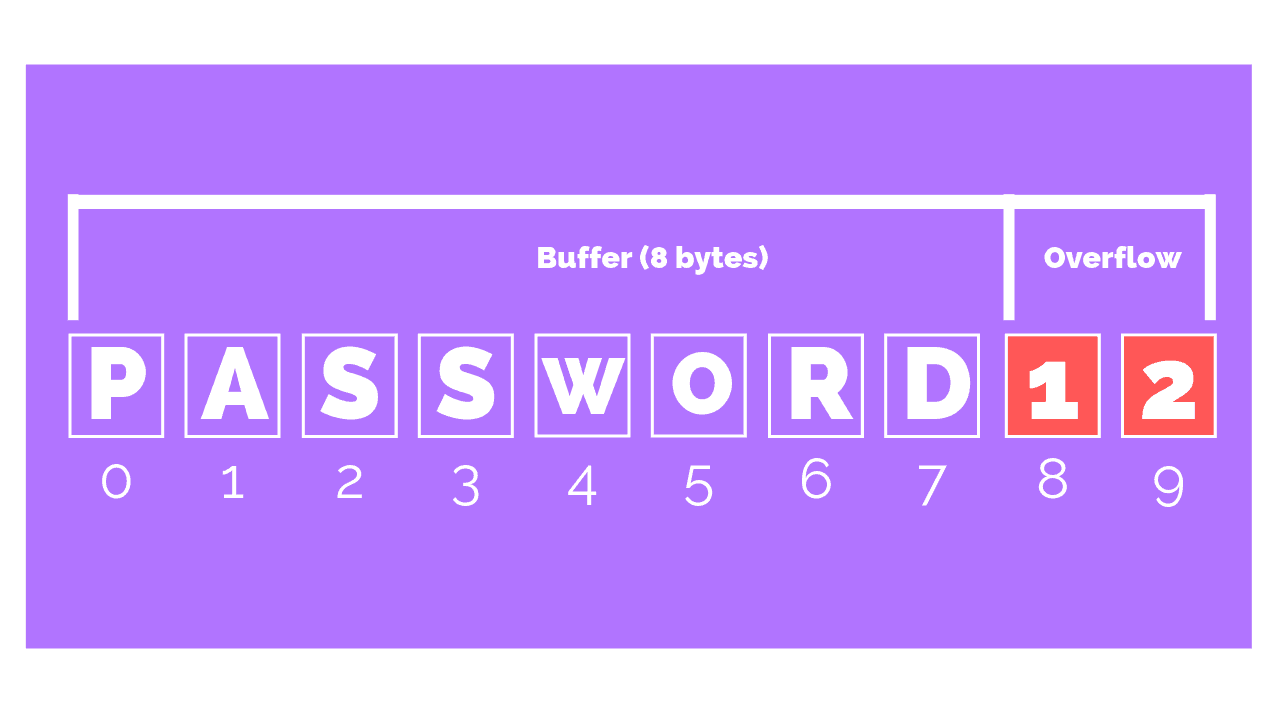
How To Prevent A Buffer Overflow Attack
A buffer overflow is one of the best known forms of software security vulnerability and is still a commonly used cyber attack. You can prevent a buffer overflow attack by au...
-
How To Prevent A Distributed Denial Of Service (DDoS) Attack
Distributed denial of service attacks continues to increase in size, frequency, and duration. According to a report from the Kaspersky Lab, DDoS attacks grew 80% in the firs...
-
What Is A Security Operations Center?
Cyber attacks are becoming ever more pervasive in our daily lives. As a result, businesses must shift their mindset to monitoring these threats in real-time. That’s wh...
-
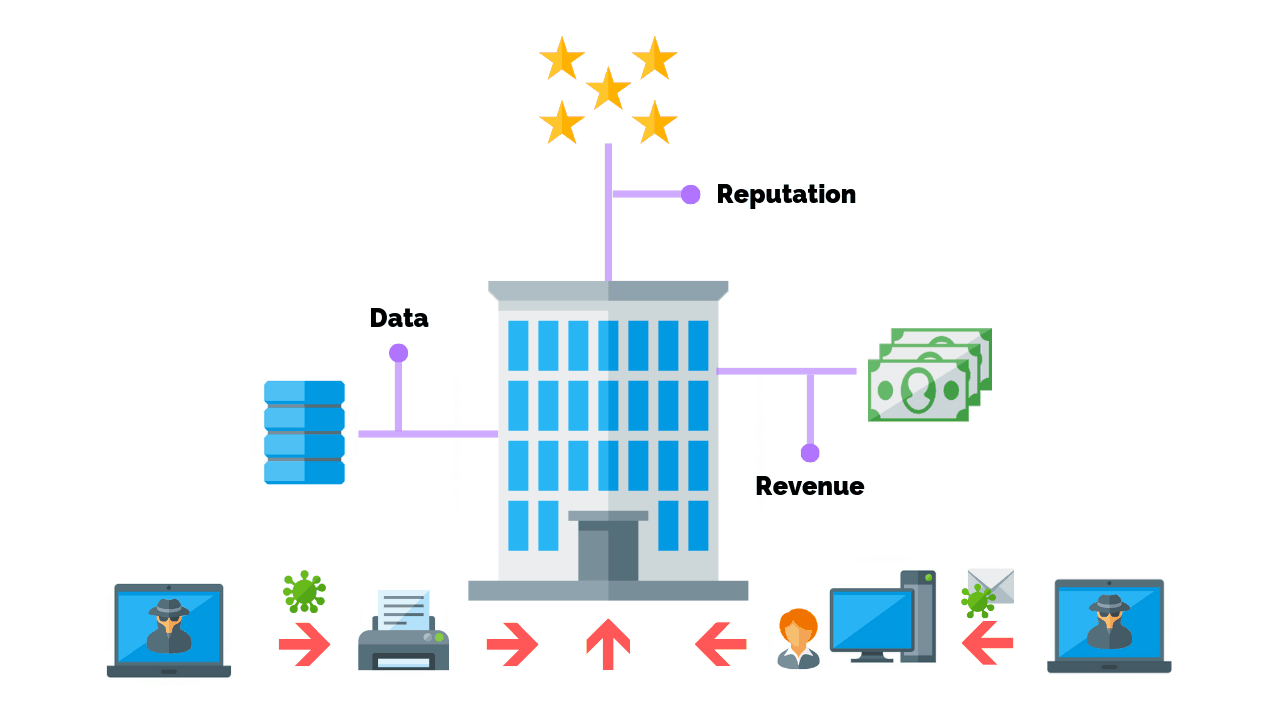
What Is Network Security? (Benefits & Types Explained)
Chances are you’ve heard of the most common vulnerabilities, and how a breach can lead to financial loss or damage to an organization’s reputation. Truthfully, t...
-
How To Perform A Successful HIPAA Risk Assessment
Cyber security, specifically ransomware, continues to be a concern for healthcare professionals with 69% believing they are at risk for a data breach. In fact, recent securi...
-
The 3 Types Of Security Controls (Expert Explains)
Security controls play a foundational role in shaping the actions cyber security professionals take to protect an organization. There are three main types of IT security con...
-
How To Prevent The Top Cyber Attacks In 2022
Cyber attacks and threats are constantly evolving, with 350,000 new malware signatures detected every day. While cyber attacks and threats are an ongoing fight, they can be ...
-
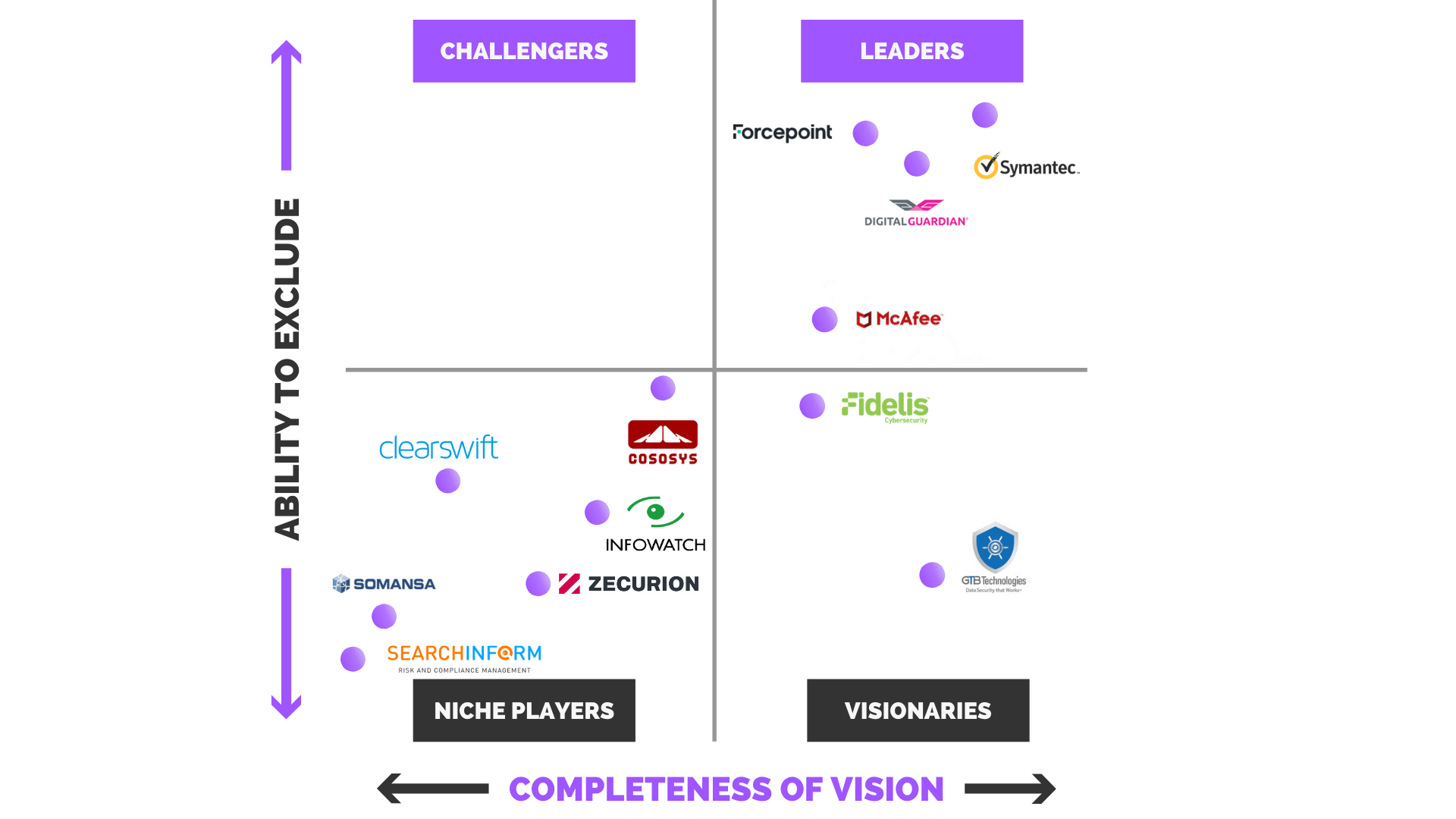
The Best Data Loss Prevention Vendors (An Expert Review)
Sensitive data is highly sought after by threat actors who look to sell personal data, health information, corporate secrets, and other valuable data on the black market. In...
-
How To Prevent Ransomware Attacks: An Expert Guide
Ransomware attacks grew 350% in 2018 reaching a total of 812 million infected devices and have been a serious concern for cities, hospitals, schools, and government agencies. As a ...
-
NIST 800-171 Incident Reporting Compliance Requirements
One thing is hard to argue in today’s complex cyber world: Cyber incidents are part of doing business. Chances are, your organization’s data will be&mdash...
-
-
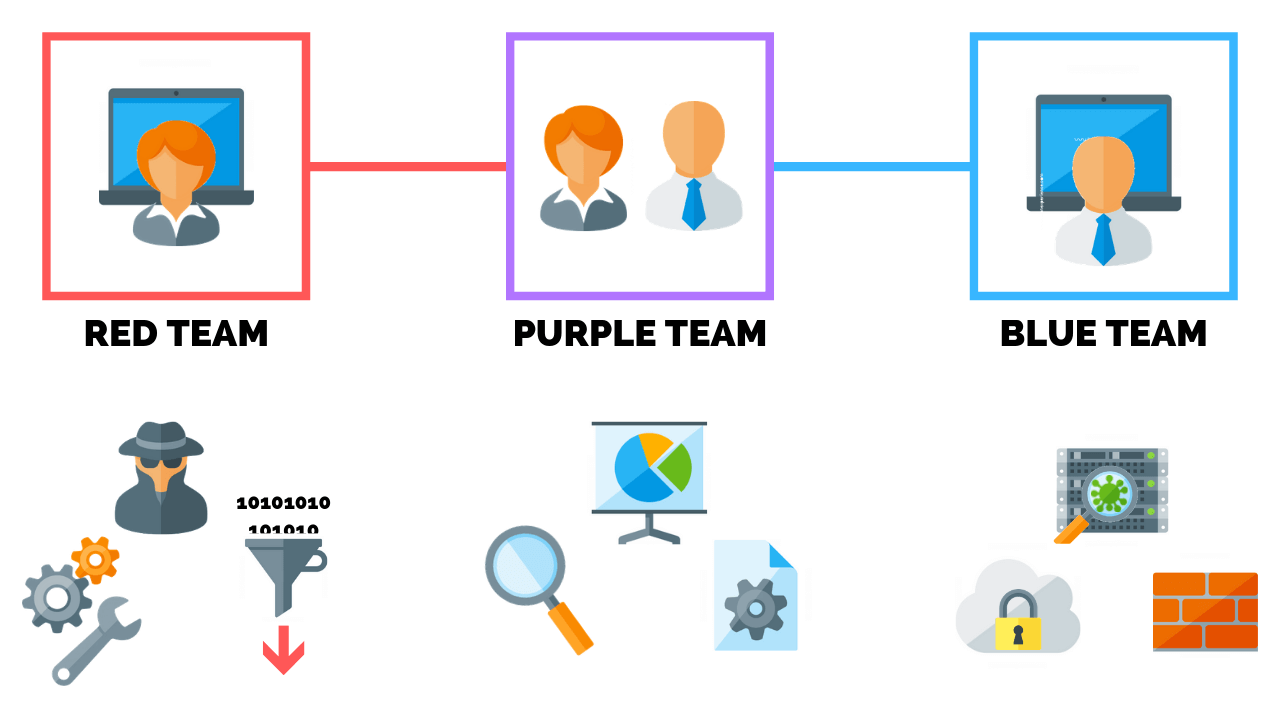
Red Team VS Blue Team: What’s The Difference?
Red and blue teams are more than just Halo references and army techniques. In fact, these teams play an important role in defending against advanced cyber attacks that threaten bus...
-
Common Types Of Network Security Vulnerabilities
Only 14% of small businesses rate their ability to mitigate cyber risks, vulnerabilities and attacks as highly effective. This is partly because network security vulnerabili...
-
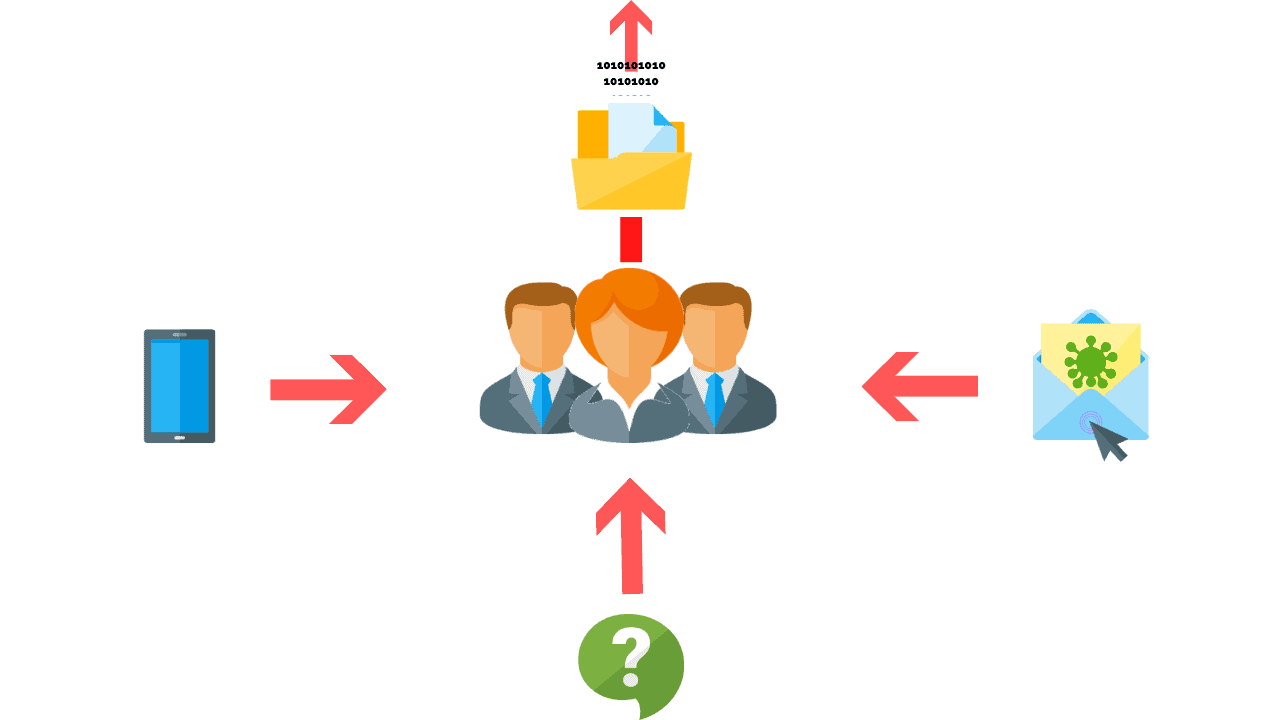
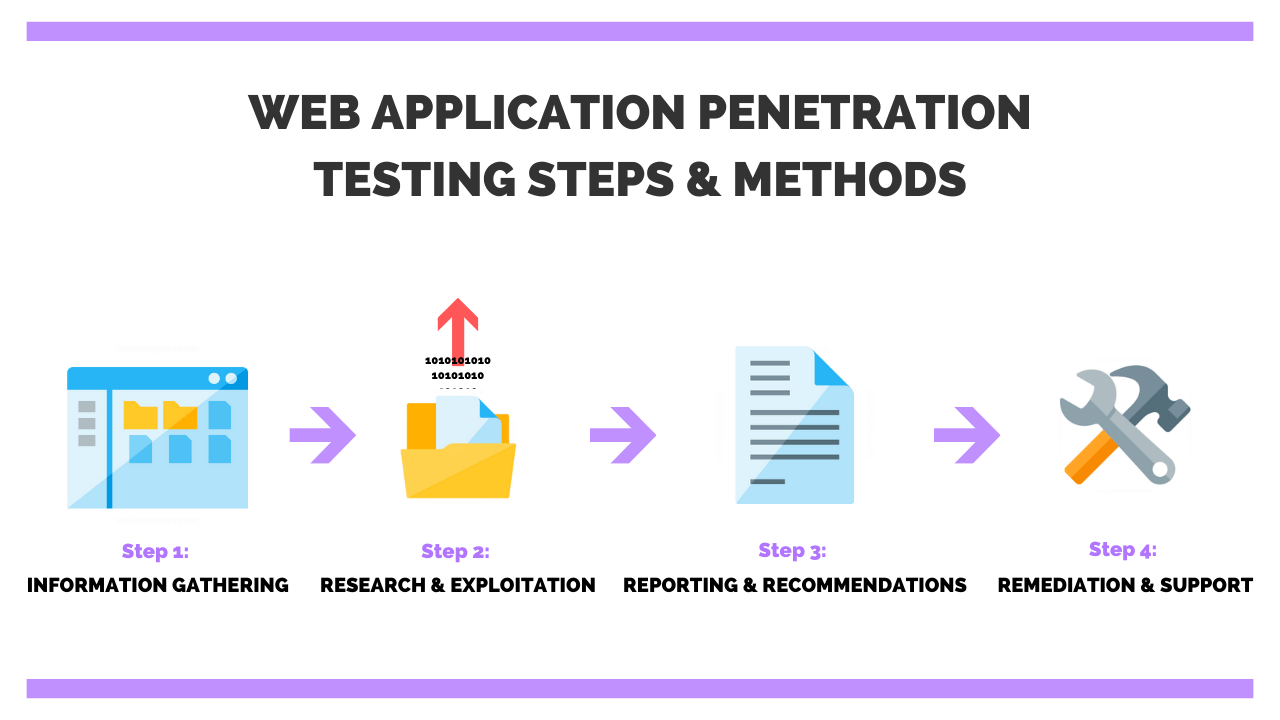
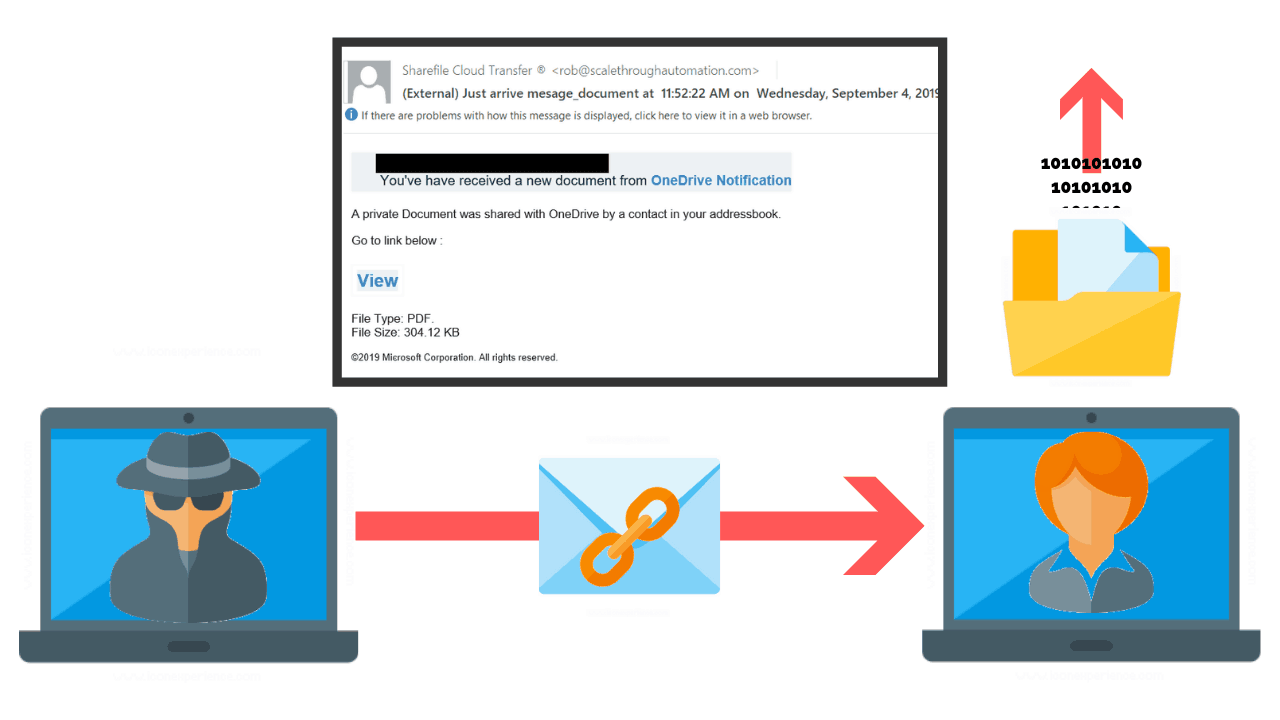
How To Create An Email Phishing Campaign In 8 Steps
Knowing how threat actors think is fundamental to preventing cyber attacks from compromising systems and networks. This is especially true since 21% of ransomware attacks ar...
-
What Is A Smishing Attack? (And How To Prevent It)
98% of cyber attacks rely on social engineering to collect sensitive data or gain access to system(s) and network(s). This is because phishing campaigns, like Smishing, are ...
-
What Is A Vishing Attack? (And How To Protect Against It)
Social engineering is the number one method used by threat actors to collect sensitive data or gain access to systems and networks. According to some security professionals Voice P...
-
10 Cyber Security Trends You Can’t Ignore In 2021
In this article, we offer our perspective on the top 10 cyber security trends in 2021. Our team of IT security experts have spent hundreds of hours researching and analyzing...
-
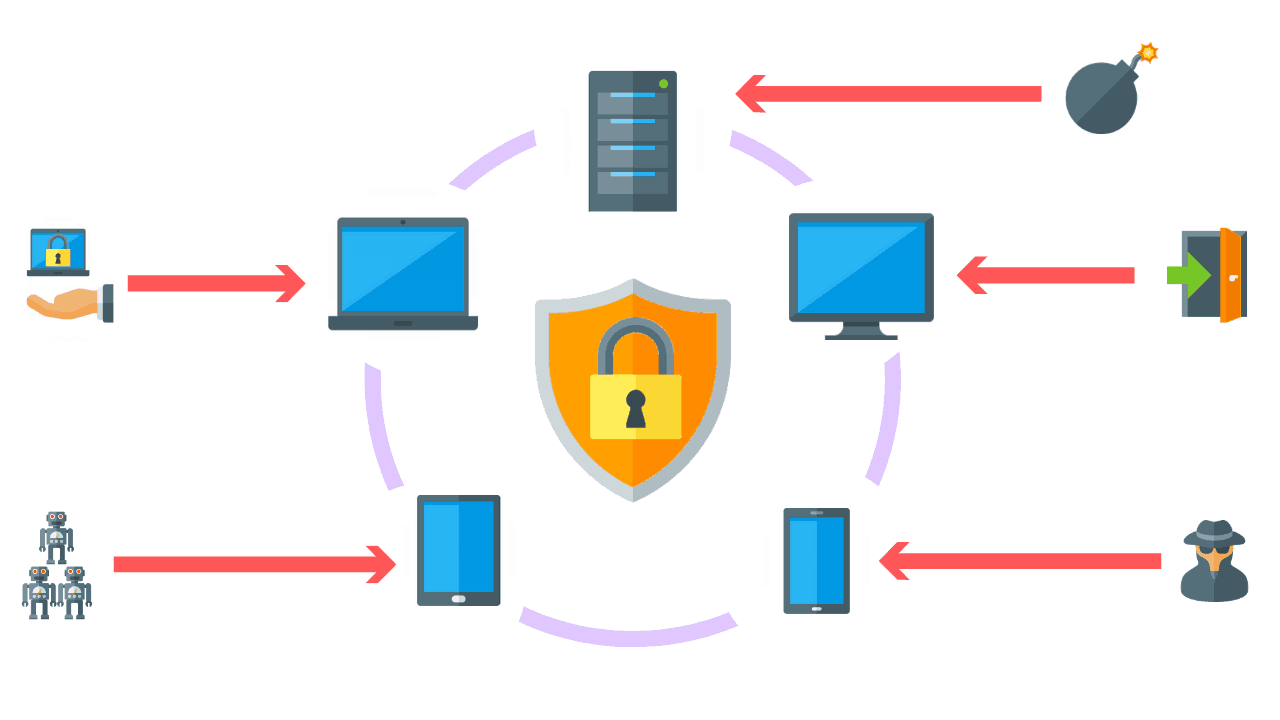
What Is Endpoint Detection And Response? (And Why It’s Important)
Endpoints today pose a significant security risk to businesses. One reason is that hackers have learned how to inject code into the operating system and its underlying appli...
-
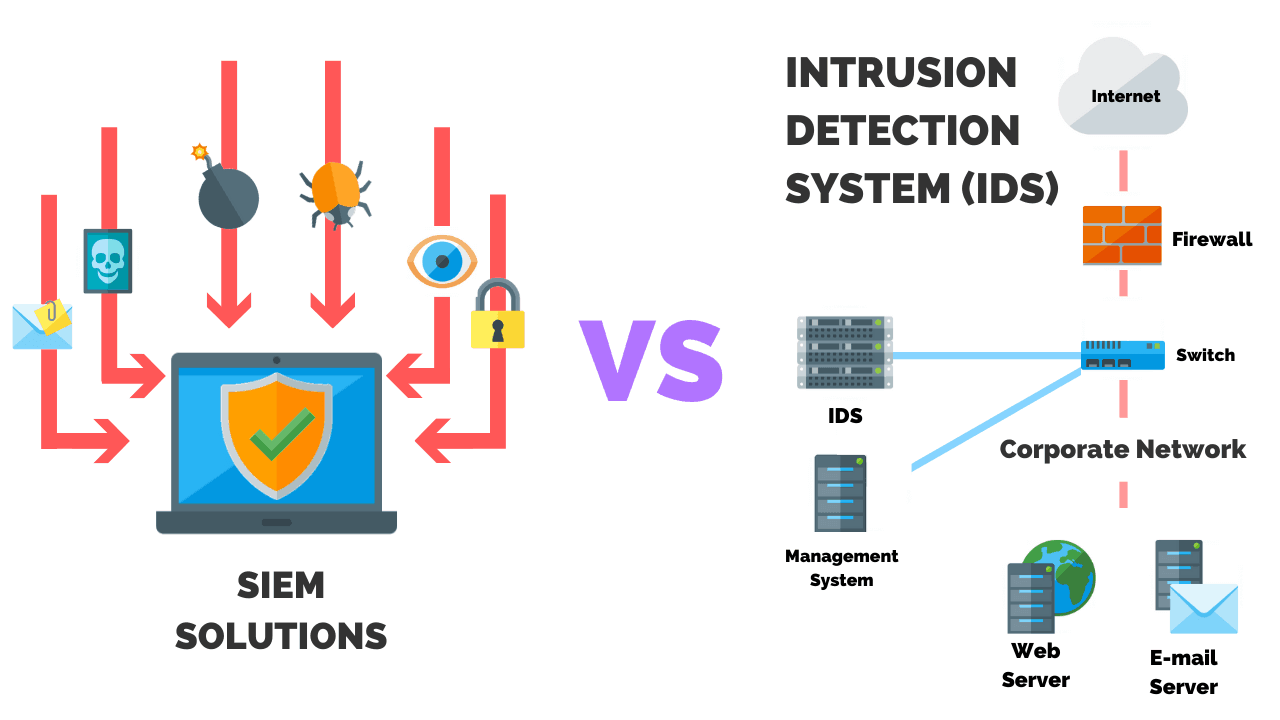
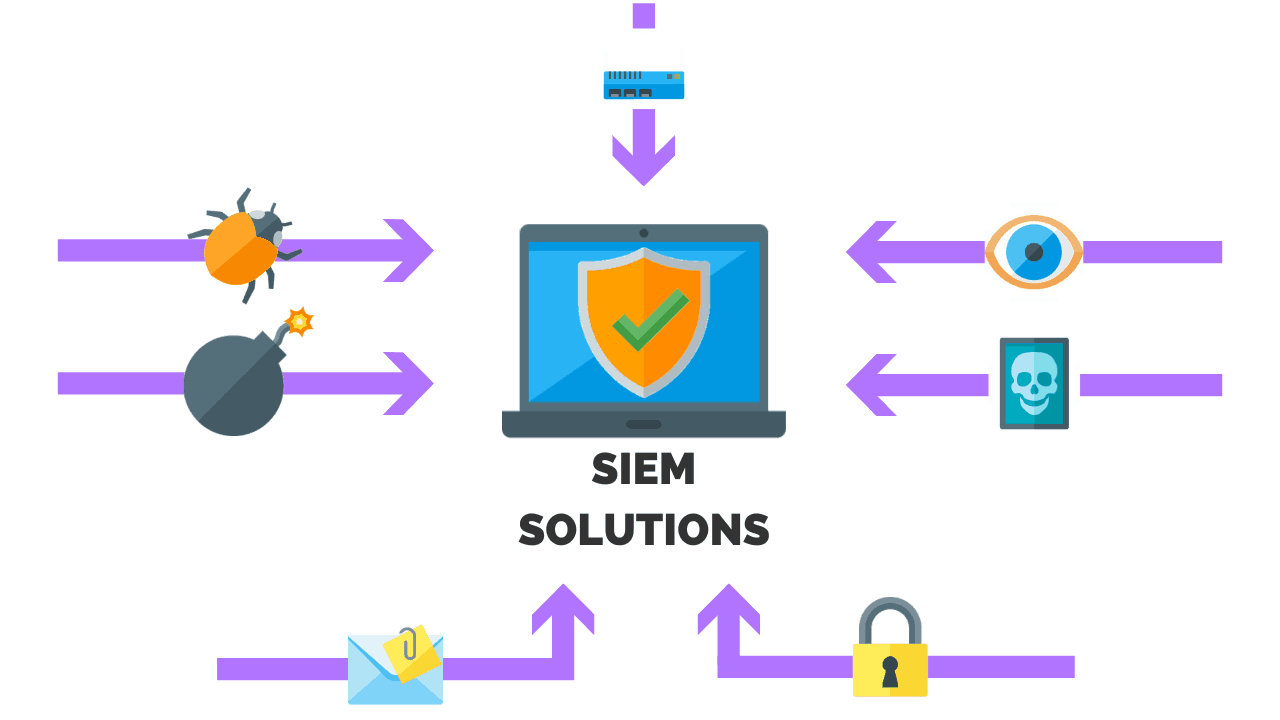
SIEM VS IDS: What’s The Difference?
In a world with ever-evolving technology comes ever-evolving threats. Awareness of the various types of security controls, their differences, and how they work to protect your busi...
-
-
What Is A SIEM Solution? Benefits, Tools, & Strategies
Organizations today are faced with the tremendous challenge of securing their data as they leverage the internet to conduct business. Why the challenge? Along with th...
-
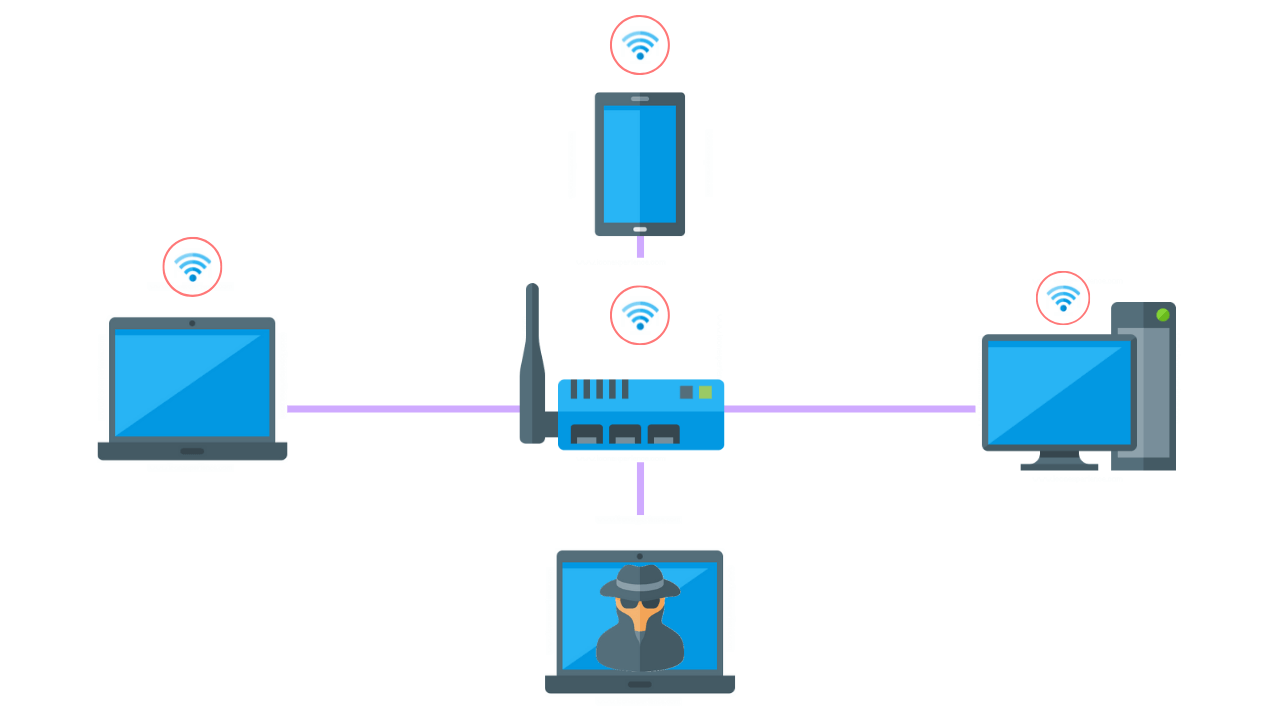
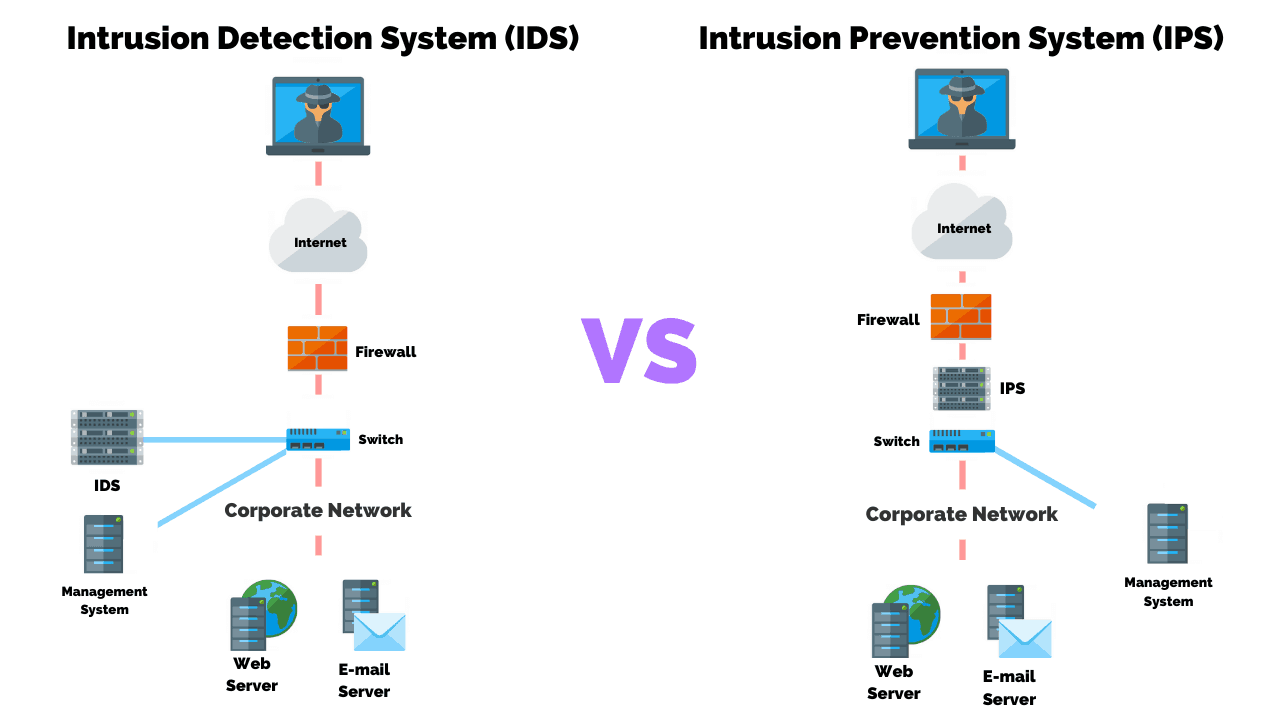
Intrusion Detection VS Prevention Systems: What’s The Difference?
The main difference between an intrusion detection system (IDS) and an intrusion prevention system (IPS) is that an IDS is used to monitor a network, which then sends alerts when s...
-
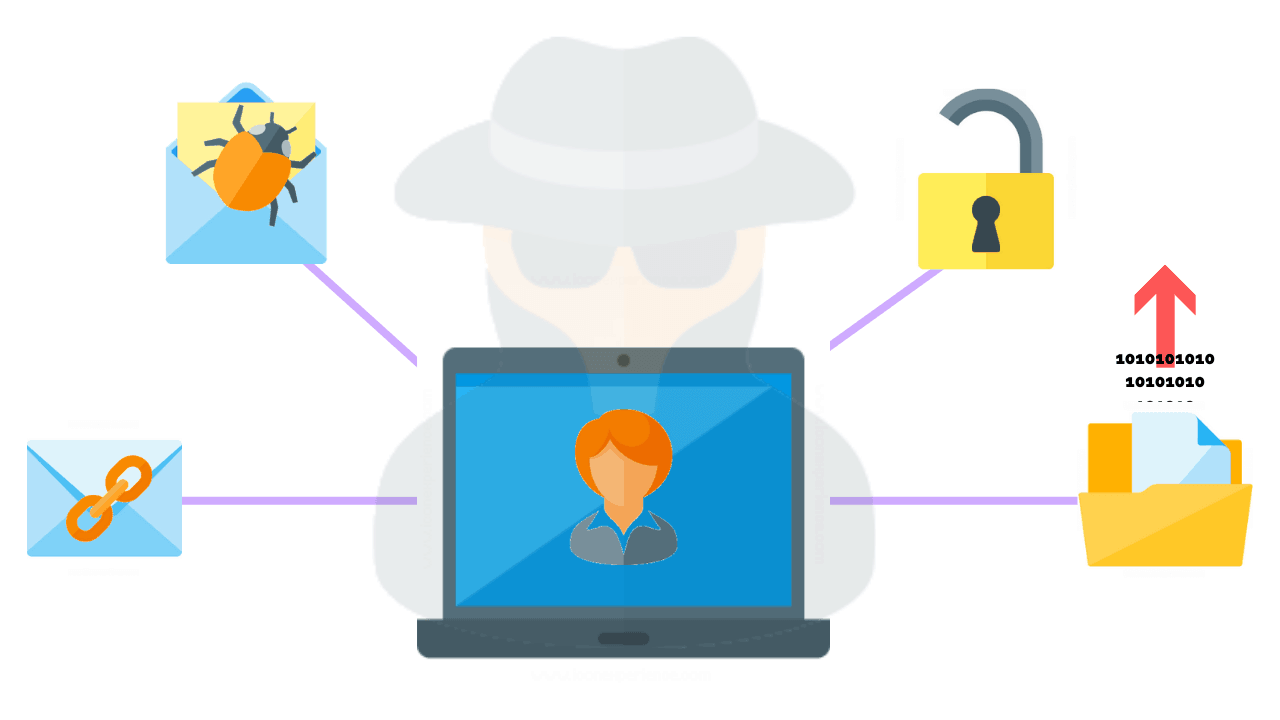
What Is A Phishing Attack? (And How To Prevent Them)
Users are often the “weakest link in the chain” when it comes to a company’s network because social engineering attacks are designed to exploit human vulnerabilit...
-
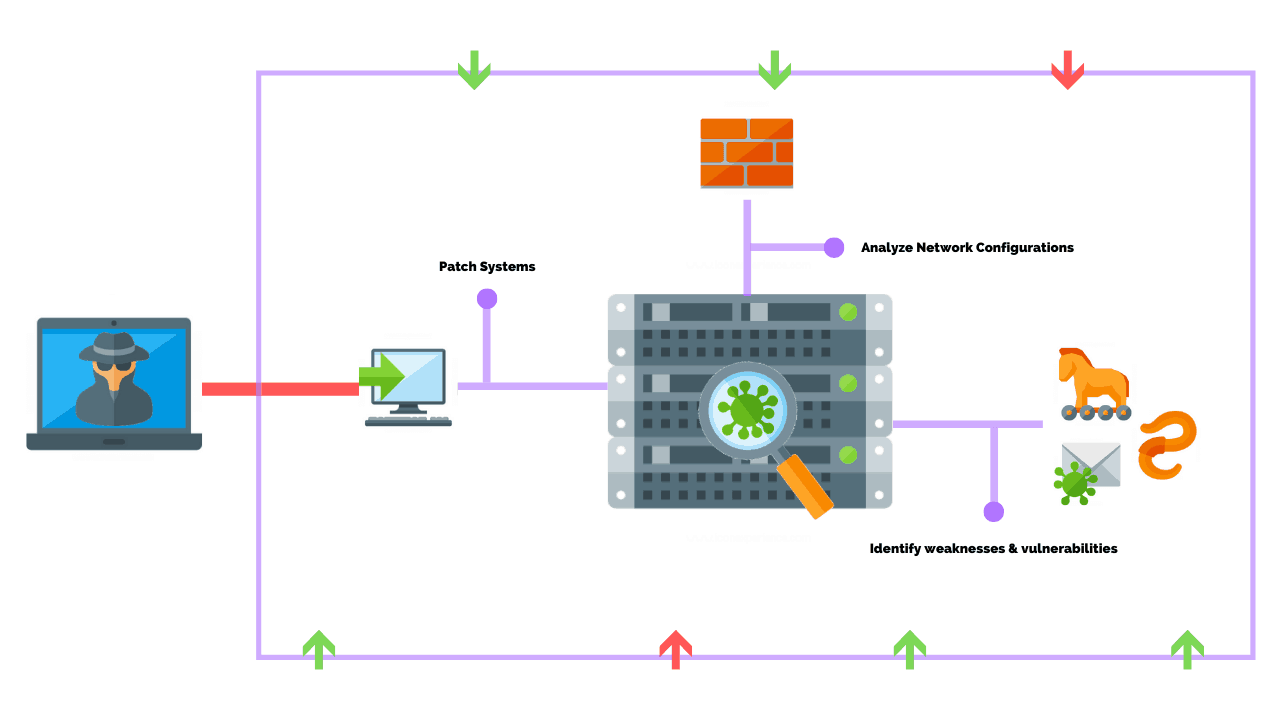
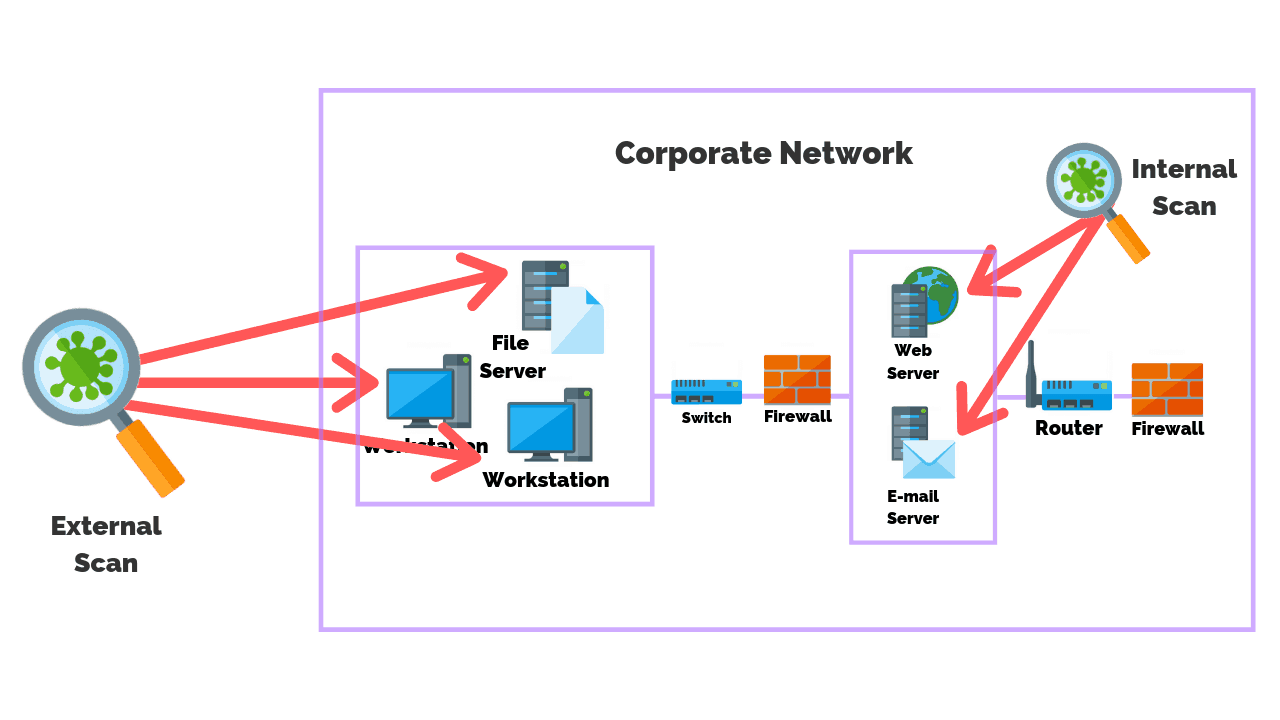
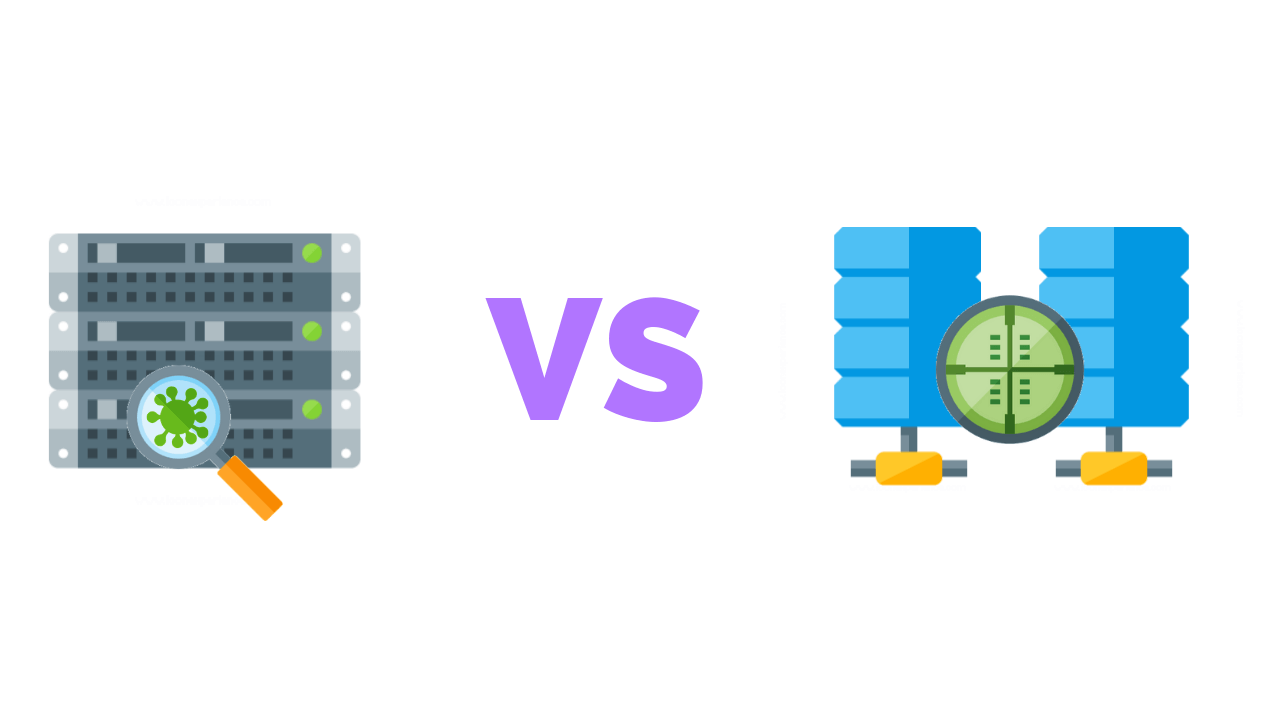
Internal VS External Vulnerability Scans: What’s The Main Difference?
Learn about PurpleSec’s fully managed vulnerability management services. In a world with ever-evolving technology comes ever-evolving threats and performing vulne...
-
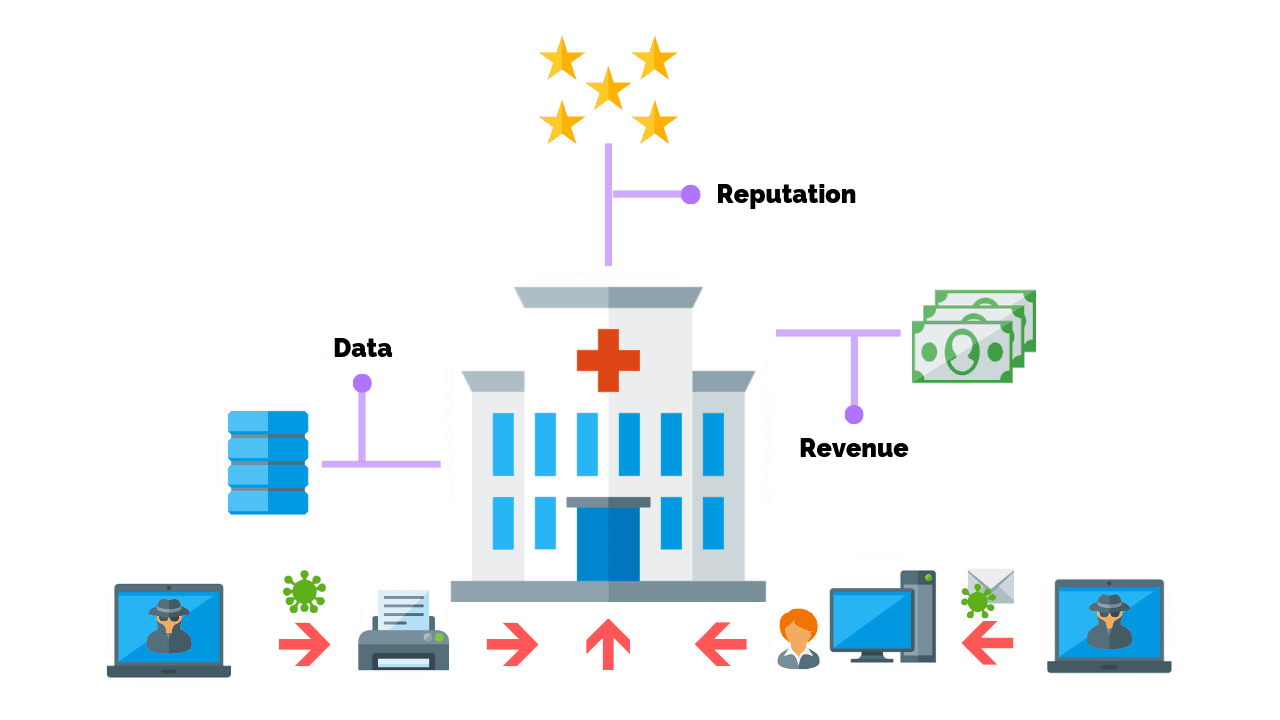
19 Healthcare Cyber Security Statistics You Need To Know In 2020
Recent statistics showing trends in cyber security threats to the healthcare industry are a cause for concern. Because healthcare facilities are critical, they are increasing...
-
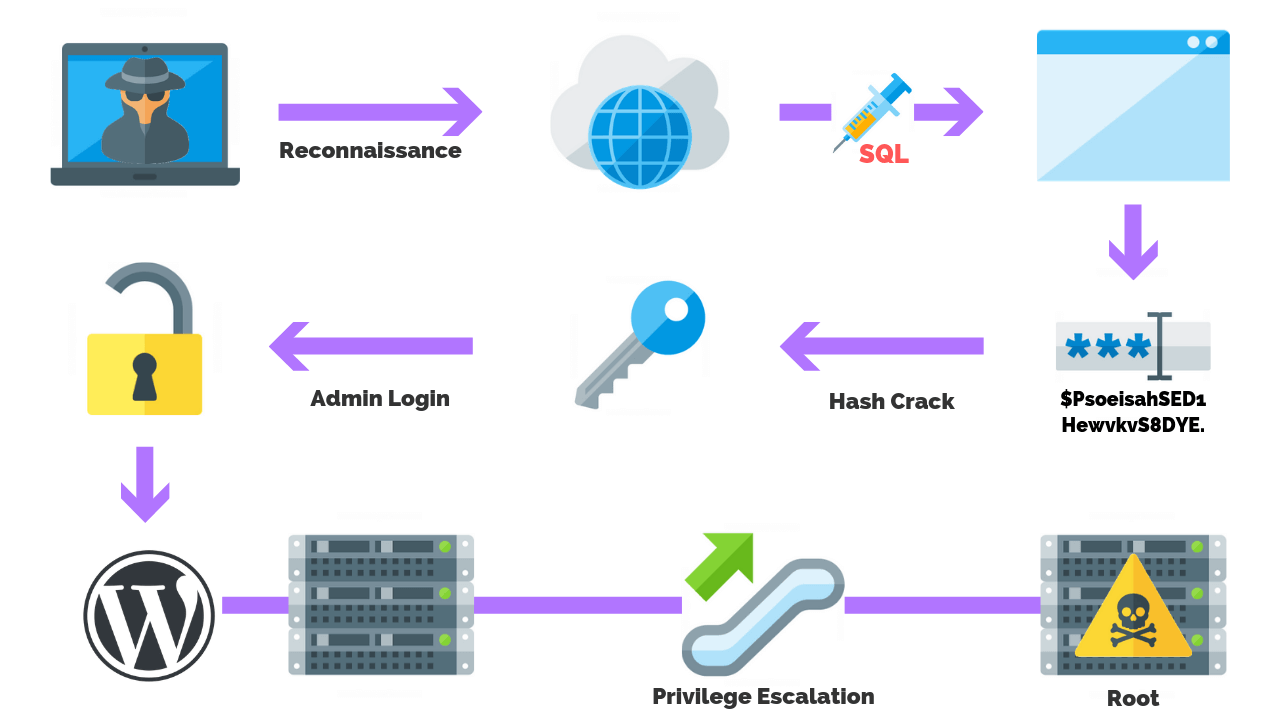
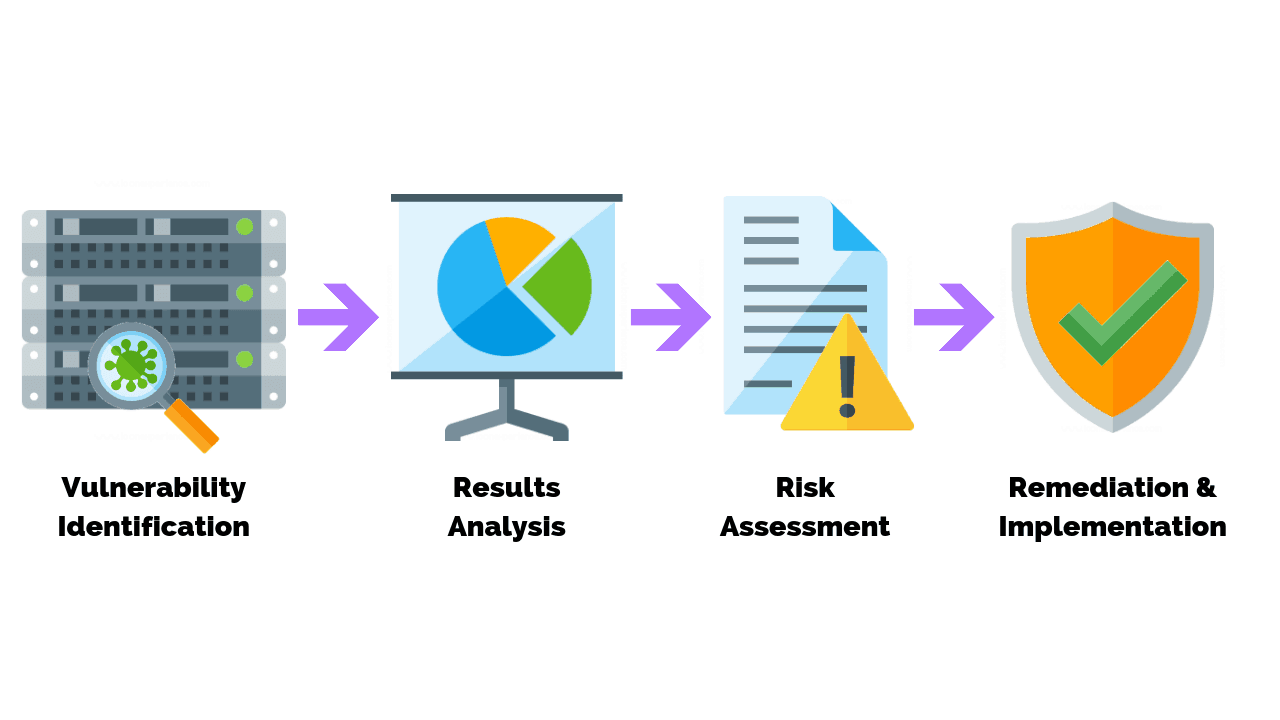
How To Conduct Vulnerability Assessment In 8 Steps
Learn about PurpleSec’s fully managed vulnerability management services. Let’s be honest, no business wants to expose itself to risk. Or, worse yet, be the ...
-
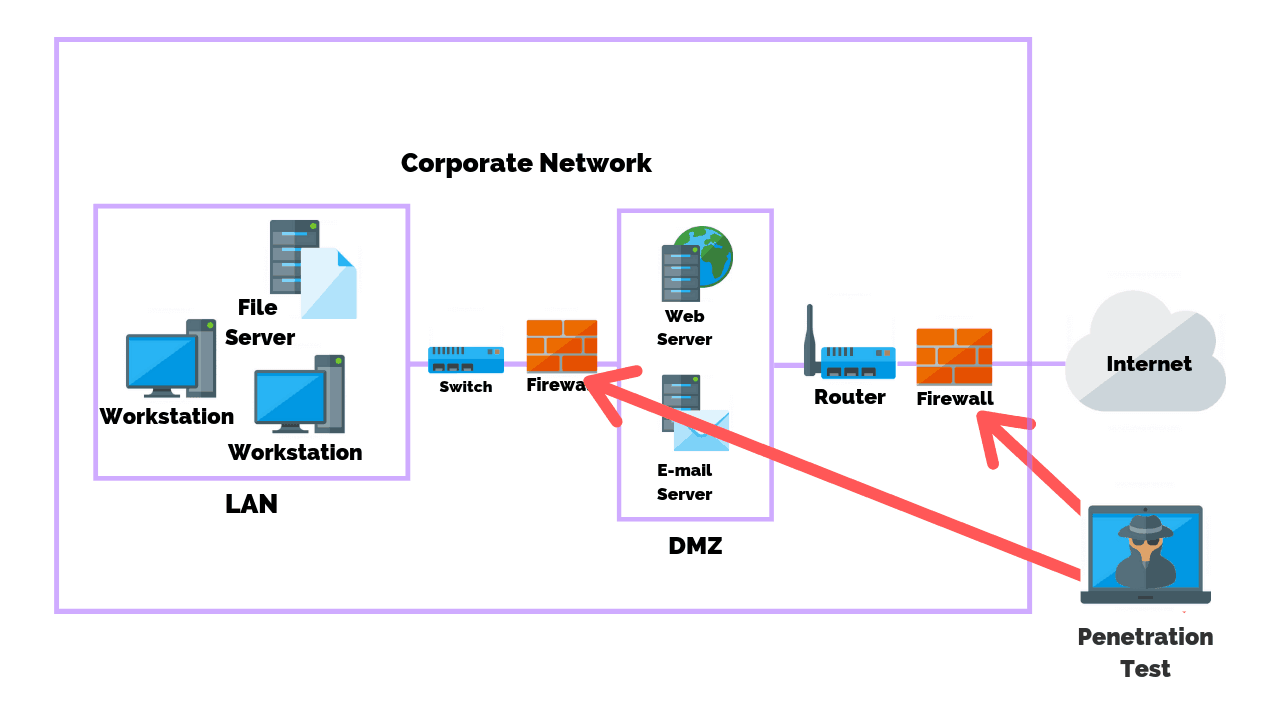
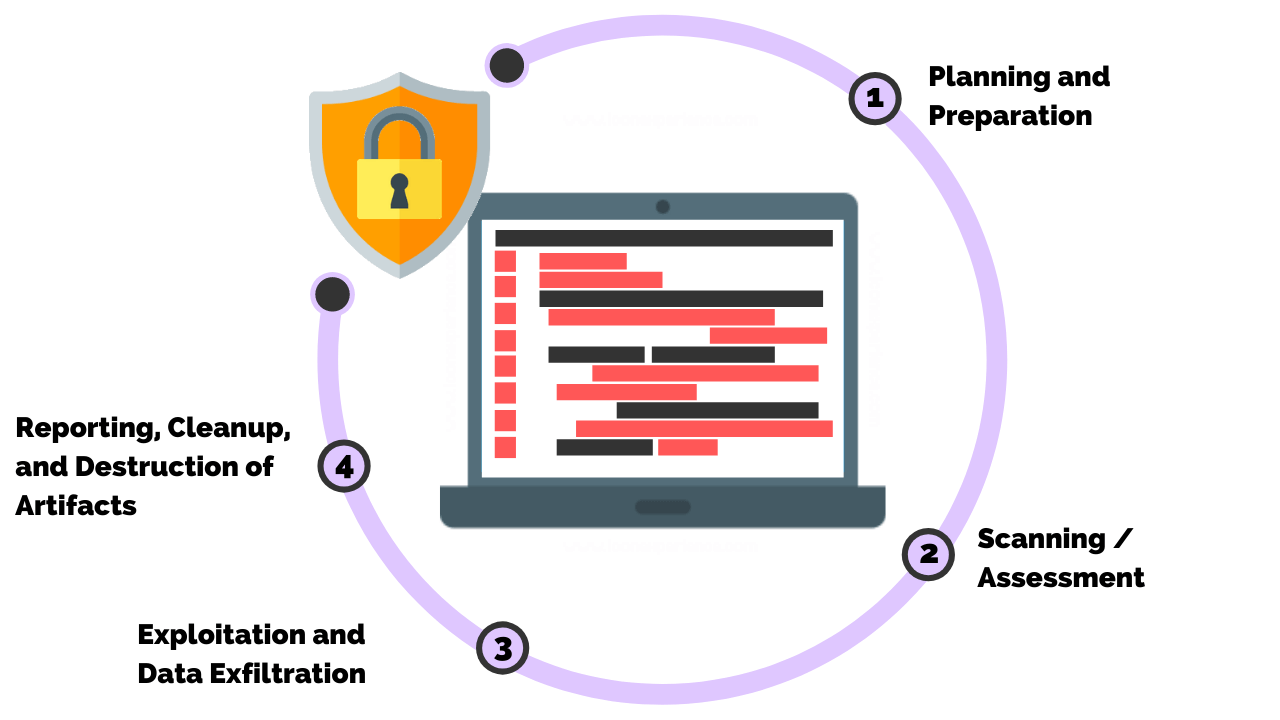
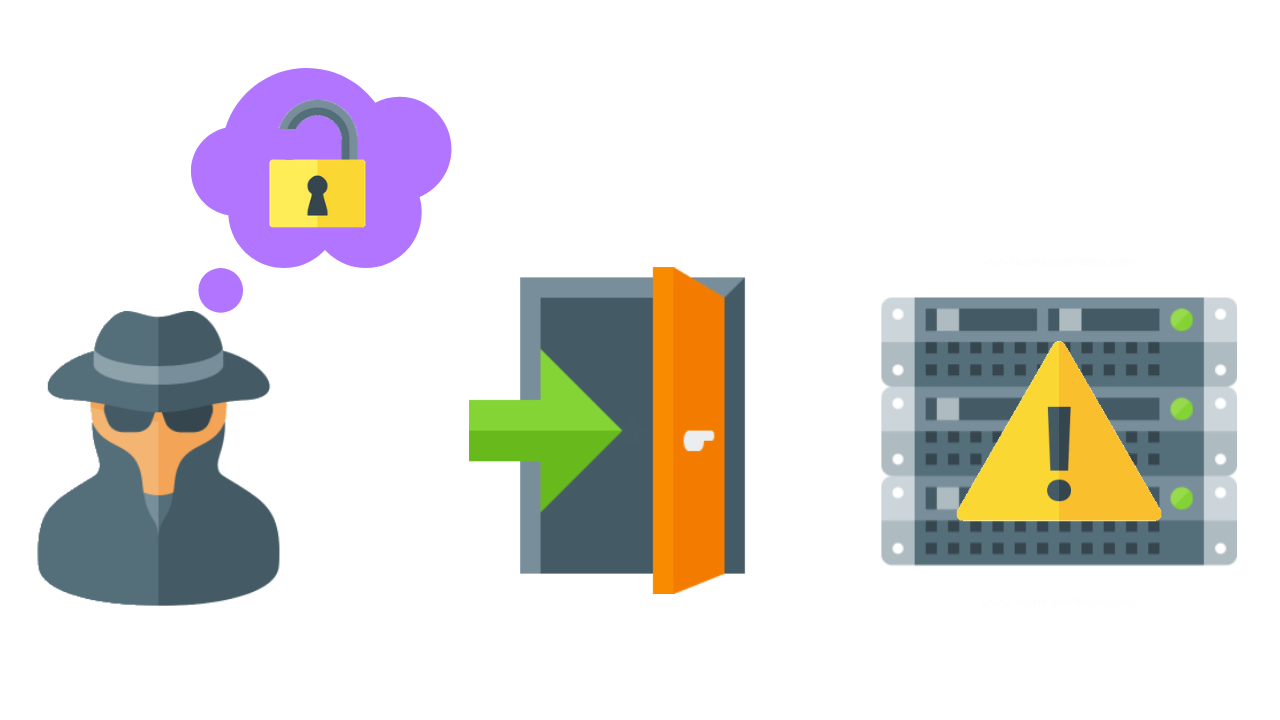
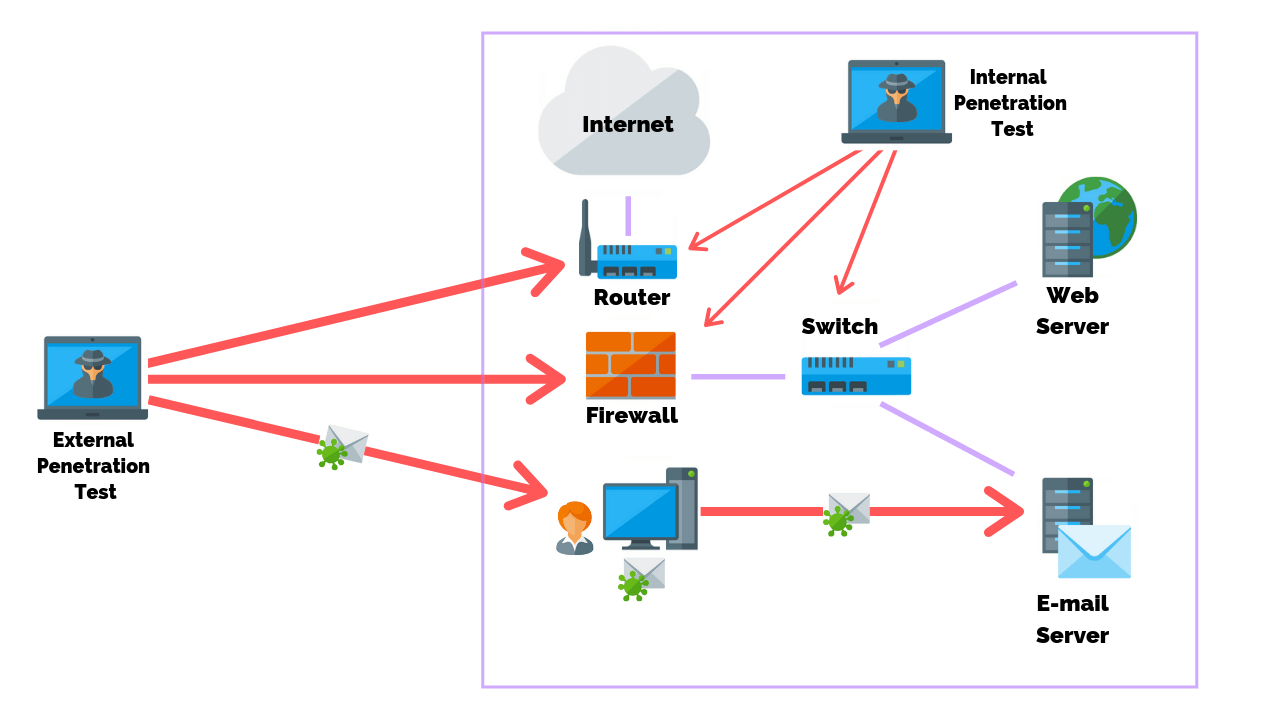
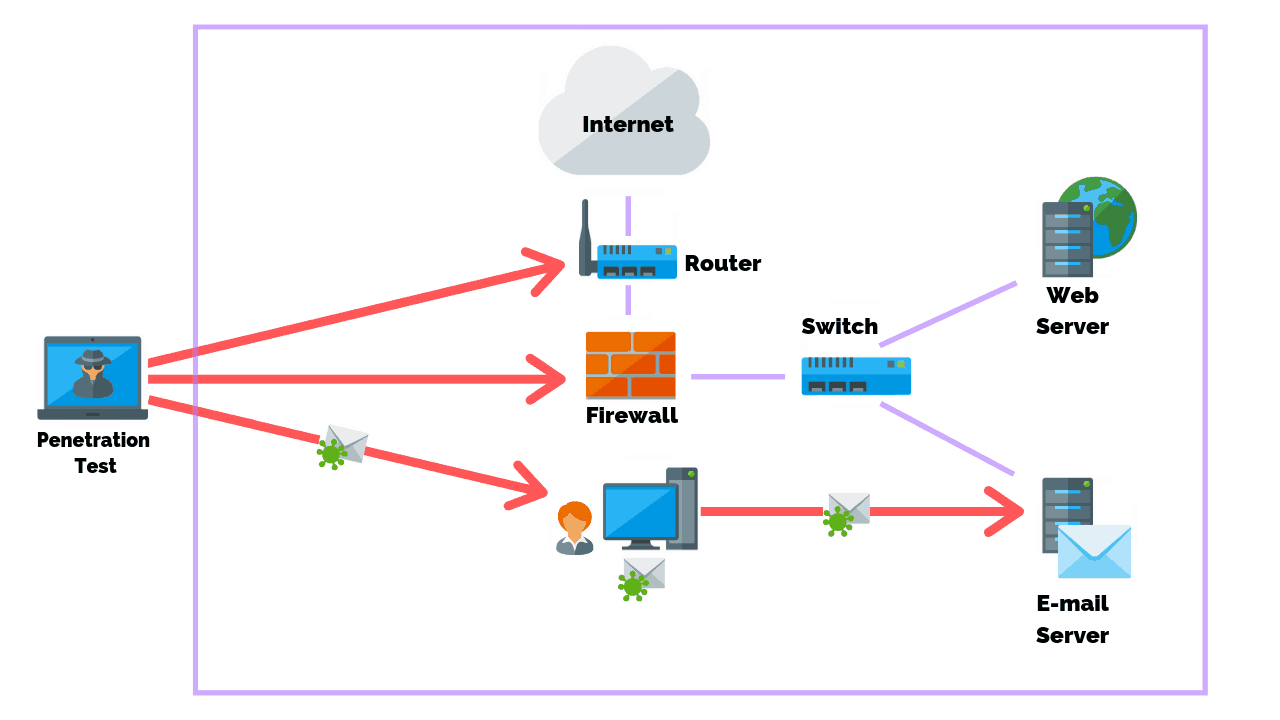
External VS Internal Penetration Test: What’s The Difference?
Penetration testing, also known as ethical hacking, is the practice of checking the security weaknesses of application software, networks, computers and devices, wireless systems, ...
-
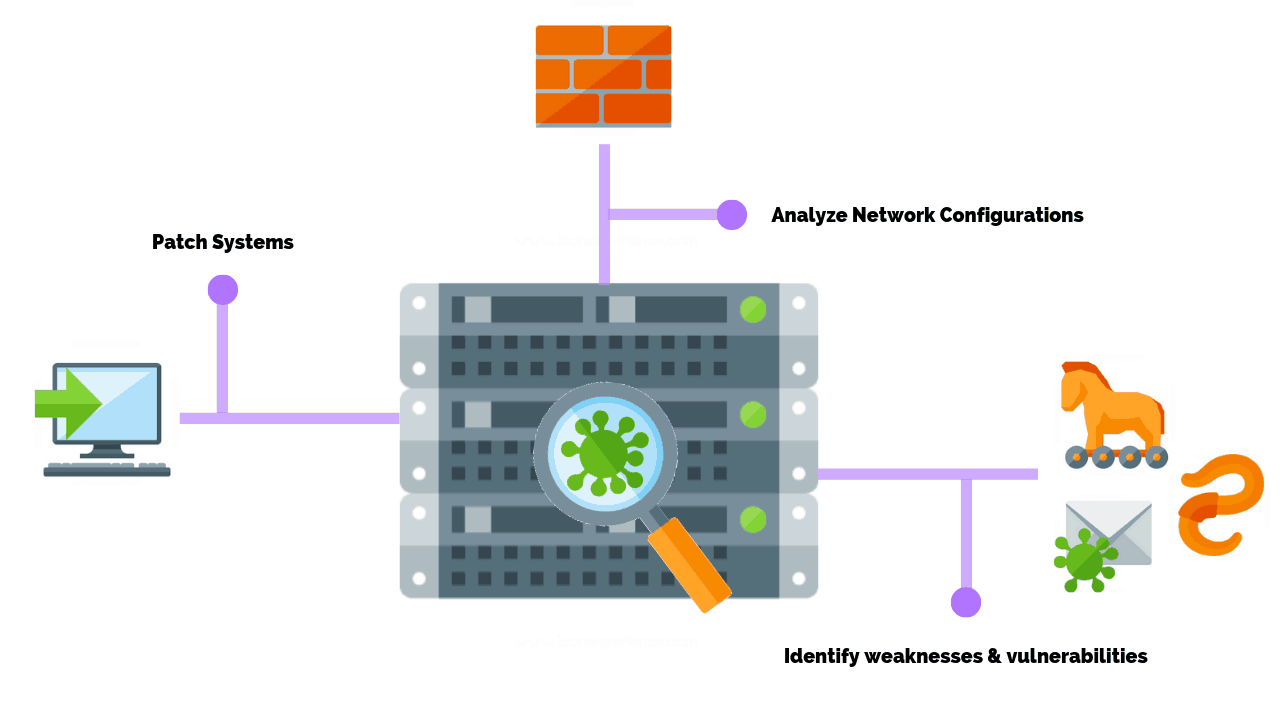
How Often Should You Perform A Network Vulnerability Scan?
Learn about PurpleSec’s fully managed vulnerability management services. A network vulnerability scan is part of the vulnerability assessment process where the ma...
-
5 Proven Network Security Tips For Small Business
While it’s true that enterprise companies are targeted by cyber attacks daily it’s actually small businesses that face the most risk of loss. This is because thr...
-