Accellion Data Breach:
What Happened & Who Was Impacted?
Contents
Accellion FTP Data Breach Explained
The Accellion file transfer application (FTA) data breach has impacted over 100 companies, organizations, universities, and government agencies around the world and continues to grow every week.
In this episode of The Breach Report, we take a look at the Accellion data breach and discuss:
- How the data breach happened.
- Who was responsible for the attack.
- What organizations have been impacted.
- How you can prevent the Accellion vulnerability.
Stay Up-To-Date On The Latest Attacks
Be the first to know when our experts release new insights on the top attacks.
You're on the list! Just one more step...
Check your email to confirm your subscription.
How Did The Accellion Breach Happen?
Threat actors combined multiple zero-day exploits and a new web shell targeting the legacy file transfer application (FTA) from Accellion.
The primary purpose behind the attack appears to be financially motivated. The threat actors extort organizations by threatening to sell their data online if a ransom payment is not made.
While Accellion did provide a patch in December 2020, it was not sufficient enough to thwart a second attack in January 2021. A subsequent patch was then released to remediate this vulnerability.
The following CVEs have been released in association with the Accellion breach:
- CVE-2021-27101 – Accellion FTA 9_12_370 and earlier is affected by SQL injection via a crafted Host header in a request to document_root.html. The fixed version is FTA_9_12_380 and later.
- CVE-2021-27102 – Accellion FTA 9_12_411 and earlier is affected by OS command execution via a local web service call. The fixed version is FTA_9_12_416 and later.
- CVE-2021-27103 – Accellion FTA 9_12_411 and earlier is affected by SSRF via a crafted POST request to wmProgressstat.html. The fixed version is FTA_9_12_416 and later.
- CVE-2021-27104 – Accellion FTA 9_12_370 and earlier is affected by OS command execution via a crafted POST request to various admin endpoints. The fixed version is FTA_9_12_380 and later.
Who Is Responsible For The Accellion Data Breach?
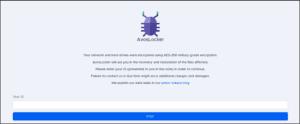
Threat researchers identified UNC2546 and UNC2582 to be behind the Accellion attacks. These threat actors have known connections to FIN11 and the CLOP ransomware gang.
Who Was Impacted By The Accellion Data Breach?
As of May 30, 2021 the Accellion data breach is known to have impacted the following organizations:
- The University Of Colorado
- Standford University
- University Of Miami
- Kroger
- University Of California
- Qualys
- Singtel
- QIMR Berghofer Medical Research Institute
- Royal Dutch Shell
- HealthNet
- Washington State
- The Reserve Bank of New Zealand
- Australian Securities and Investments Commission
- Bombardier
- Transport For NSW
- Flagstar Bank
- Trinity Health
- University of Maryland
- California Health & Wellness
- Trillium
- Arizona Complete Health
- Centene
- Goodwin Procter
- Jones Day
- Harvard Business School
- CSX
- City of Toronto
- CalViva Health
Free Security Policy Templates
Get a step ahead of your cybersecurity goals with our comprehensive templates.

How Can You Prevent The Accellion Vulnerability?
It is strongly recommended by security professionals that you do not use the file transfer appliance app provided by Accellion. This application is unsupported by the vendor and will no longer receive security patches.
If you continue to use this application past its end-of-life date then you are placing your organization at serious risk of compromise.
Article by
Share This Article
Our Editorial Process
Our content goes through a rigorous approval process which is reviewed by cybersecurity experts – ensuring the quality and accuracy of information published.
Categories
The Breach Report
Our team of security researchers analyze recent cyber attacks, explain the impact, and provide actionable steps to keep you ahead of the trends.