PurpleSec's Leadership
Meet The Team Securing Small Businesses
Hear From Our Customers
Our clients place their trust in us to help them make the right cybersecurity decisions. But don’t just take our word for it.

Virtual CISO
How PurpleSec Improved And Matured Select * Associates, Inc.'s Security Posture

Penetration Testing
How PurpleSec Helped ConvertKit Improve Security For Half A Million Customers

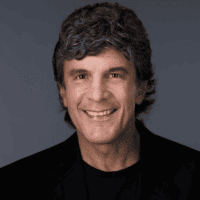
Vulnerability Management
Explore Our Security Solutions
Ready To Get Secure?
Reach Your Security Goals With Affordable Solutions Built For Small Business