The way that code is developed has changed immensely over the past decade, yet for some reason, companies still believe that implementing security the same way we did it ten years ago should be sufficient.
Think of it this way, we would never purchase tons of different services that we might need as part of our software stack and later ask for their price, yet it is a standard practice to develop all the different features in an application and then ask ourselves if our product is secure.
Implementing continuous penetration testing into your security program in the development cycle from the beginning is not more work. In fact, it enables organizations to develop secure code and discover vulnerabilities more quickly.
Techniques to mitigate these potential breaches can then be developed and implemented across the organization.
As a result of these proactive measures organizations can focus on constantly improving their defensive security controls versus building plans and defenses once the damage is done.
With continuous testing, you are able to receive constant simulations of how a breach can look like, what are your weak points and apply what you’ve learned in your defense strategies.
Sample Network Pen Test Report
What should a penetration test report include? Download our sample report to learn.

What Is Continuous Penetration Testing?
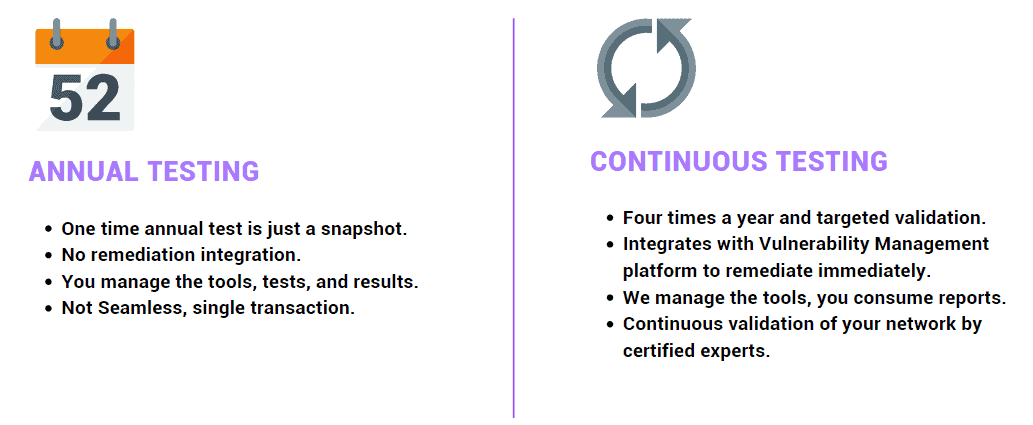
 There are many definitions of continuous penetration testing. At PurpleSec, we believe conducting a penetration test at least quarterly means you’re continuously assessing your security posture.
There are many definitions of continuous penetration testing. At PurpleSec, we believe conducting a penetration test at least quarterly means you’re continuously assessing your security posture.
There are, of course, many different definitions as to what “continuous” means and which frequency of testing is the best for your organization.
However, at its core, you can say that you are performing continuous penetration testing if your organization is constantly aware of the security status of your application, service, or network system.
When we say “Continuous Penetration Test” we refer to a thorough security assessment to discover security flaws in your application, service, or network conducted by an offensive certified security professional (OSCP).
What Continuous Penetration Testing Isn’t
Continuous Penetration Testing does not mean pointing a scanner at an environment or API looking for vulnerabilities. It is also not a checkbox, but a learning opportunity and a mapping tool for the security posture of your environment.
Most importantly, Continuous Penetration Testing is not a barrier in your software development cycle. And this is often something that is quite argued in development teams.
The most frequently asked question once an organization decides to implement continuous penetration testing is:
“How do I fit security in the picture without slowing down the development process?”
The best answer to this is that you can plan it, which puts your organization in control, therefore the development teams communicate better and can address the security challenges in a timeline that works for the organization.
On the other side, by conducting penetration tests only once or twice a year, you are kept in the dark about the security status of your applications, services, or networks for a longer period.
This means you can anticipate bigger security issues to be identified, which would then require more work for the development teams, shorter deadlines to implement the newly required security controls, and unavoidable rearrangement of the security development plan.
Why Is Continuous Penetration Testing Important?
With new technologies constantly being developed and AI on the rise, threat actors are now not just using standard tools and methodologies but they are importing AI tools into their arsenal, tools like ChatGPT to build and automate attacks more effectively than before.
To combat this growing threat, a more thorough and continuous assessment of your cyber security posture is a must.
The main benefits of continuous penetration testing include:
- Cost-Effective
- Increase Visibility
- Meet Compliance Requirements
- Reduces Cyber Risk
Cost-Effective
You can plan the mitigation of findings, and most likely a smaller amount of work will be required therefore not whole teams need to be engaged in fixing the security findings and you can seamlessly implement the fixes as tasks in your sprint. Continuity also allows for better budget planning.
Increases Visibility Of The Security Posture
With continuous penetration testing, you are constantly informed about the security status of your environment.
This provides more insight into what additional controls need to be implemented in your defense strategy which allows you to continuously and simultaneously build your defense as you assess your posture.
Learn More: How To Improve Visibility In Cyber Security
Helps To Meet Compliance Requirements
Continuous assessments provide more evidence, more findings, and more reports, therefore, removing the pressure of not complying with security standards and regulations since you’ll be constantly up to date.
Reduces The Risk Of Successful Attacks
The key to staying ahead is always data, organizations need to know more about their environment than threat actors do. Continuous penetration testing enables that.
Free Penetration Testing Policy
Skip the policy-writing hassle with our ready-to-use penetration testing policy template.

Why Annual Penetration Testing Isn’t Enough
With the emerging threat landscape, threat actors are constantly on the lookout for zero-day vulnerabilities.
We are experiencing an increasing number of security researchers, new technologies are constantly being developed and implemented in our technology stack and organizations are releasing new features more frequently.
This just expands the attack surface and accelerates development.
Now the question to ask is “Are you building securely?”
Unfortunately, annual penetration tests can’t answer that, especially not at the pace that things are being built today.
When Should You Consider Continuous Penetration Testing?
An organization can determine when it needs continuous penetration testing by evaluating its overall security posture and risk profile.
Some factors that can indicate a need for continuous penetration testing include:
- High-Value Assets: Continuous penetration testing can assist in identifying and resolving vulnerabilities that could be exploited by attackers if an organization has to protect valuable assets, such as sensitive data or vital infrastructure.
- Compliance Requirements: Organizations that work in regulated fields like healthcare or finance may have to adhere to rules that call for frequent penetration testing.
- Frequent Changes To The Network: Continuous penetration testing can assist in identifying and addressing vulnerabilities that may be introduced as a result of network changes on a regular basis.
- Previous Security Incidents: If an organization has experienced security incidents in the past, continuous penetration testing can help identify and remediate vulnerabilities that may have contributed to those incidents.
- Risk Appetite: if an organization has a high-risk appetite, continuous penetration testing will give them the ability to have a more thorough understanding of the organization’s security posture, thus reducing the risk of attacks.
Ultimately, the decision to implement continuous penetration testing should be based on an organization’s overall security goals and risk management strategy.
Best Practices For Implementing Continuous Penetration Testing
While you may want to dive right into a continuous penetration testing process it’s important to first explain a few best practices around how to implement this program for your organization.
- Determining The Frequency
- Set Clear Objectives And Goals
- Use Both Manual And Automated Techniques
- Regular Review Of Testing Processes
Determining The Frequency
The frequency in which a pentest should be performed is usually based on how often do you develop new features or make significant changes to our network/codebase/infrastructure and how critical is the new feature that is being developed.
Always think of the security implications and the possible worst-case scenarios.
Set Clear Objectives And Goals
Before deciding to implement continuous security penetration testing answer these questions:
- With what kind of data are we dealing with?
- What are the key flow processes that we want to be tested?
- What are some scenarios that, if they materialize, would be disastrous for our company?
Write these down and start from there.
It is also quite important to set the communication tone at the beginning of the engagement.
- What is it that you’re looking for from this pentest?
- How can the pentest team help you?
Establish communication channels between both teams so you can get the most value out of it.
Use Both Manual And Automated Techniques
Get an understanding of the methods and techniques that are going to be used throughout the pen test. Look for a service that uses a combination of both manual and automated testing techniques.
For example, automated penetration testing will scan and attempt to exploit vulnerabilities found on the network or application.
However, a manual technique is required to identify out-of-the-box security policies set in say Microsoft or security misconfigurations that may be present.
Regular Review Of Testing Processes
The client’s environment changes and so should the testing process. Look for penetration testing services that model APTs using the Mitre ATT&CK framework.
Since you want to collect opinions from both your offensive and defensive teams, it is crucial to establish collaborative threat modeling.
$35/MO PER DEVICE
Enterprise Security Built For Small Business
Defy your attackers with Defiance XDR™, a fully managed security solution delivered in one affordable subscription plan.
Wrapping Up
Penetration testing is essential because it identifies system vulnerabilities before hostile actors can take advantage of them.
Regular testing guarantees that any flaws are found and fixed right away, shielding the system and its users from potential attacks.
For any organization’s digital assets to remain secure, ongoing penetration testing is crucial.
PurpleSec allows you to build a powerful and continuous penetration testing program.
This allows teams to focus on more important issues and develop programs focused on reducing human error without worrying about the broader threat landscape.
Article by