Vulnerability Management Services
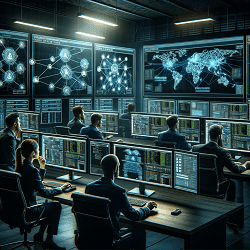
Continuously Monitor And Remediate Vulnerabilities
Our Approach To Vulnerability Management
Manage and analyze vulnerabilities and risk in one place.

Deliver Immediate Value
A rapid time-to-value solution that’s easy to use and has minimal requirements for implementation, configuration or training.

Leverage The Latest Intelligence
Expert-defined Remediation library that immediately delivers the right fix for any vulnerability to speed up risk remediation.
Custom-Built For Your Needs
Easy to configure with the ability to automate as much or as little of the vulnerability management lifecycle as you need.

Vulnerability Management Plans & Pricing
Includes no long-term contracts, no upfront costs, 1st month free, and a 2-year price lock.
Defiance XDR™
Vulnerability Management
Manage our solution yourself.
-
Continuous Scanning
-
Automatic Patching
-
Program Support
-
Platform Support
Vulnerability Management
As A Service
We fully manage our solution for you.
-
Fully Managed By PurpleSec
-
Continuous Scanning
-
Automatic Patching
-
Custom Security Policies
The Challenges Of
Vulnerability Management
As IT environments become more complex and the attack surface expands the potential for risk grows. Organizations at all sizes struggle to prioritize and mitigate vulnerabilities at scale across highly distributed architectures.
And entire vulnerability and risk management programs are now responsible for everything from hybrid and multi-cloud environments to container images and code repositories, and as well as traditional storage and network infrastructure.
Effective mitigation processes now need to span diverse teams (security operations, DevOps, application development, etc.), each with its own business mandates, unique processes, and preferred operating technologies.
Information / Data Overload
Organizations have thousands or even millions of vulnerabilities identified by their scanners without a clear understanding of where to start remediating to pinpoint real security exposures.
Slow Response
Times
Traditional approaches to vulnerability prioritization and patch management are disconnected, overlay manual and lead to too many critical vulnerabilities.
Too Many Operating Siloes
A chronic lack of collaboration between departments delays vulnerabilities being fixed and critical cyber risks being addressed in a timely fashion.
Finding A Fix Takes Too Long
With potentially hundreds of unique vulnerabilities at any given time, manually looking up the fixes or workarounds for each is too slow and time consuming for effective risk management.
How Our Vulnerability Management Services Work
Our security engineers come equipped with cutting-edge AI, ML, and enhanced threat Intelligence.
Step 1:
We send a virtual machine package, or a security device.

Step 2:
Integrates seamlessly with your existing technology stack.

Step 3:
Our tools automate prioritizing and patching based on risk.

Step 4:
You get a managed solution backed by a team of experts.
“We needed a mature and robust solution led by a team of experts that could reduce our vulnerability backlog and patching cycles across thousands of endpoints. PurpleSec’s team quickly established a framework, introduced their platform, and reduced our remediation windows well below national averages!“
– Crystal H., IT Program Manager
National Travel Insurance Provider
Vulnerability Management Solution Deployment
Reduce your organization’s risk exposure within 48 hours of deployment.
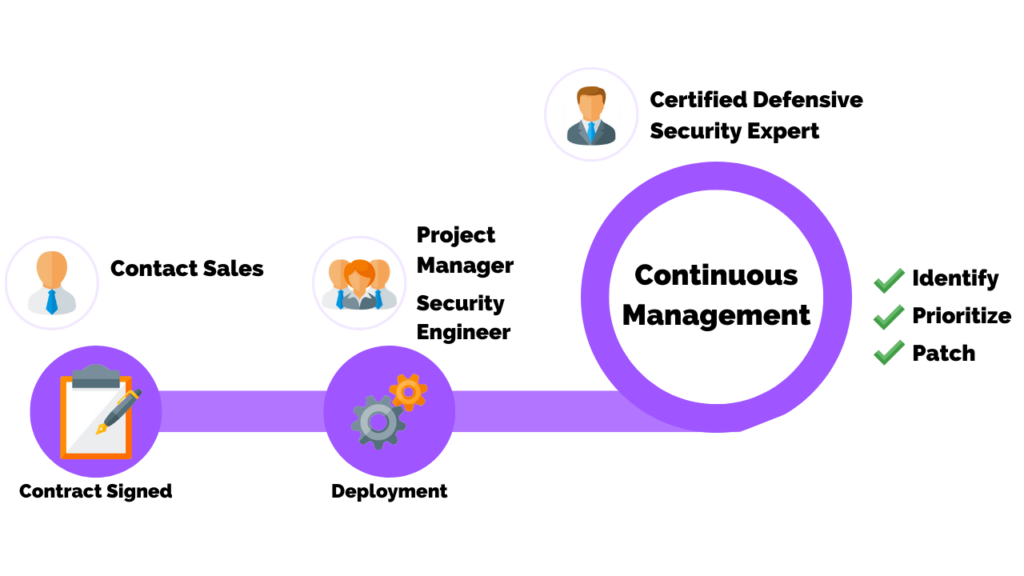
The Fastest Path To Full-Cycle Vulnerability Management
Continuous vulnerability detection and remediation in minutes, not months.
Why Choose PurpleSec’s Vulnerability Management Services?
At PurpleSec, our vulnerability management experts will establish a framework to proactively identify, classify, remediate, and mitigate vulnerabilities in applications or an IT infrastructure with the goal of reducing risk.
This approach ensures that we prioritize work on the areas of greatest risk by identifying the strengths and weaknesses of your vulnerability management program; thereby maximizing the ROI of your security initiatives.

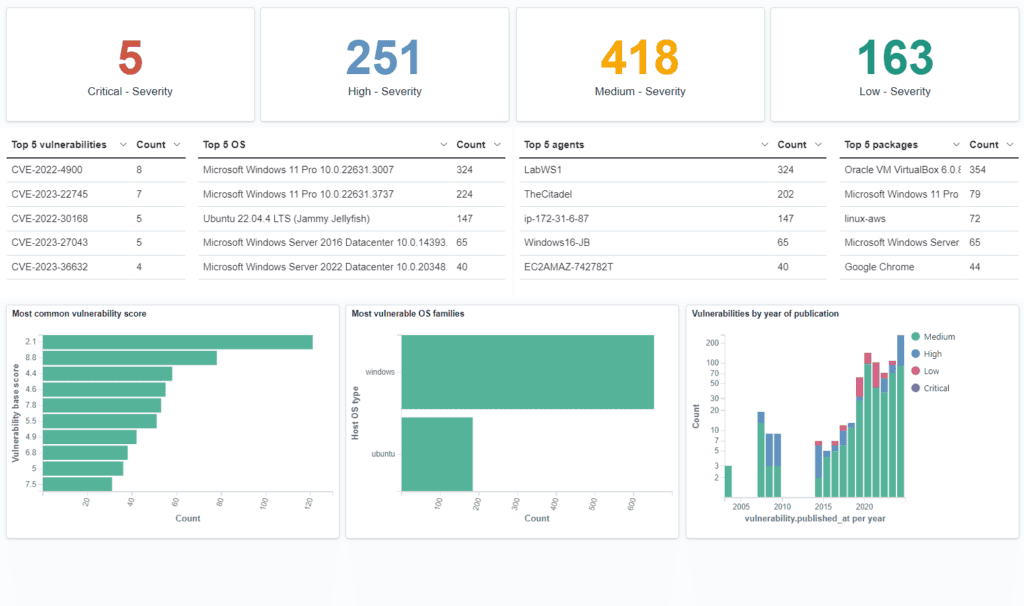
PurpleSec’s Vulnerability Risk Management Platform
Accurately prioritize vulnerabilities based on your environment, understand your actual risk aligned to your business objectives, and adapt our analytics algorithms to fit your operating requirements.
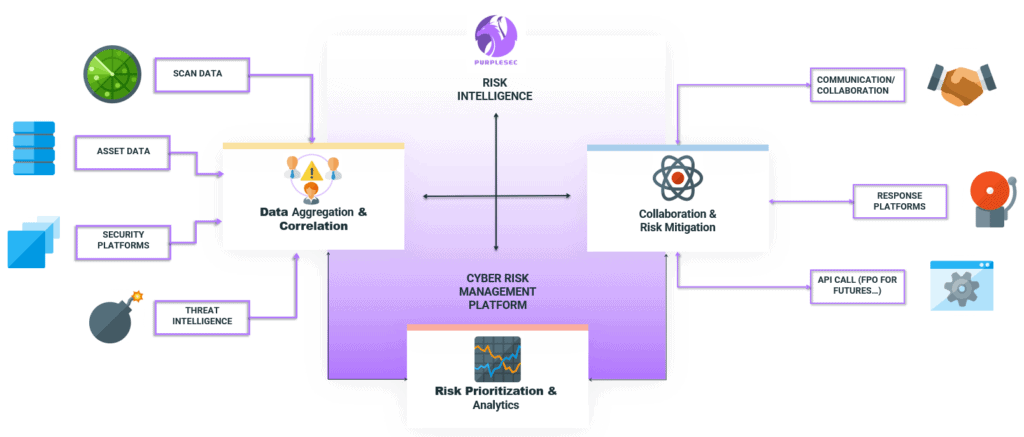
Communication And Collaboration With All Departments
PurpleSec enables Security, IT, DevOps, and Application Developt teams to manage risk together in the most effective way for their operating requirements, using their preferred toolsets. It is tightly integrated with ITSM, application development, DevOps, and deployment tools, as well as communication and collaboration platforms to orchestrate remediation processes more effectively.

Content-Aware Vulnerability Prioritization
PurpleSec analyzes relevant data from a wide range of sources, including organizational context specific to each enterprise, and delivers expert vulnerability assessment intelligence to deliver more information and better prioritization so that you understand the actual risks to your environment and how they might impact your organization.

Aggregation And Correlation Of All Data
PurpleSec integrates with any vulnerability and risk detection solution, covering servers, workstations, containers, cloud workloads, code, applications, and more. It consolidates risk analysis across infrastructure, code, applications, and cloud assets, delivering full risk visibility across every potential attack surface.

Expert-Defined Remediation Intelligence
PurpleSec automatically enriches vulnerability and risk data using our own machine learning and expert-driven engine to deliver proprietary threat intelligence* (exploits, running campaigns, threats, and usage in the world) as well as Remediation Intelligence (recommended patches, workarounds, configuration changes and mitigations).

Customizable Risk Analytics And Reporting
PurpleSec delivers extensive analytics and lets you create custom reports to serve different audiences and purposes, such as executive-level dashboards to track KPIs or detailed views into critical vulnerabilities and high priority tasks.

Automated Mitigation Playbooks
PurpleSec has an intuitive playbook builder for automating previously manual cyber risk lifecycle management and vulnerability remediation activities and tasks, reducing operating overhead and accelerating mean-time-resolution (MTTR).
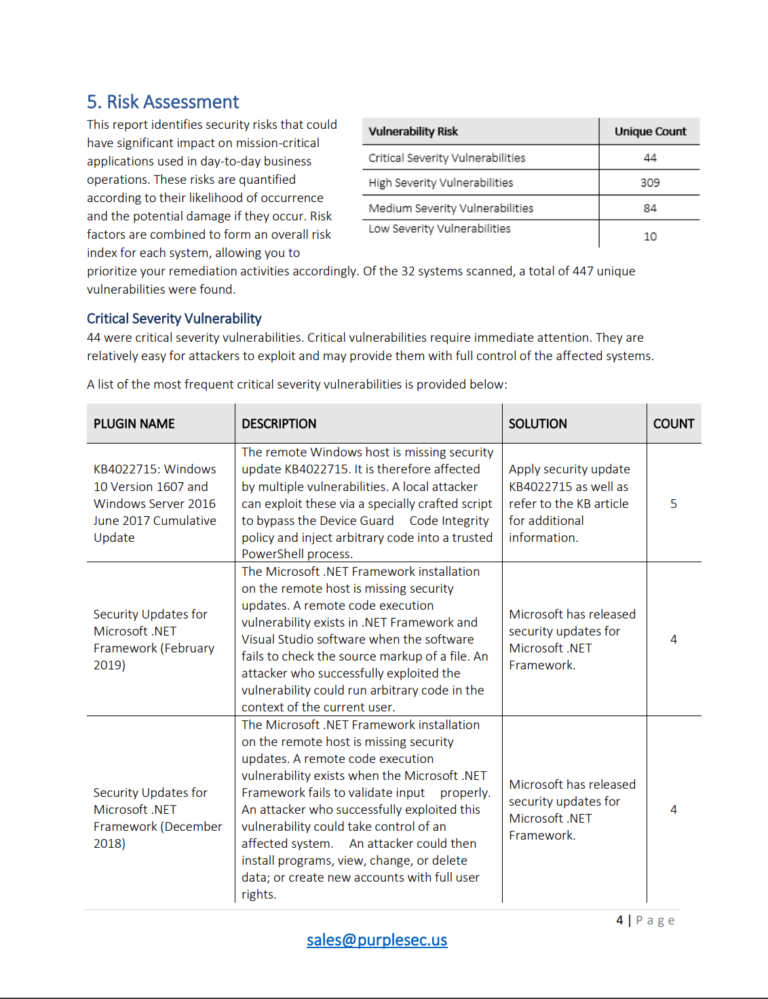
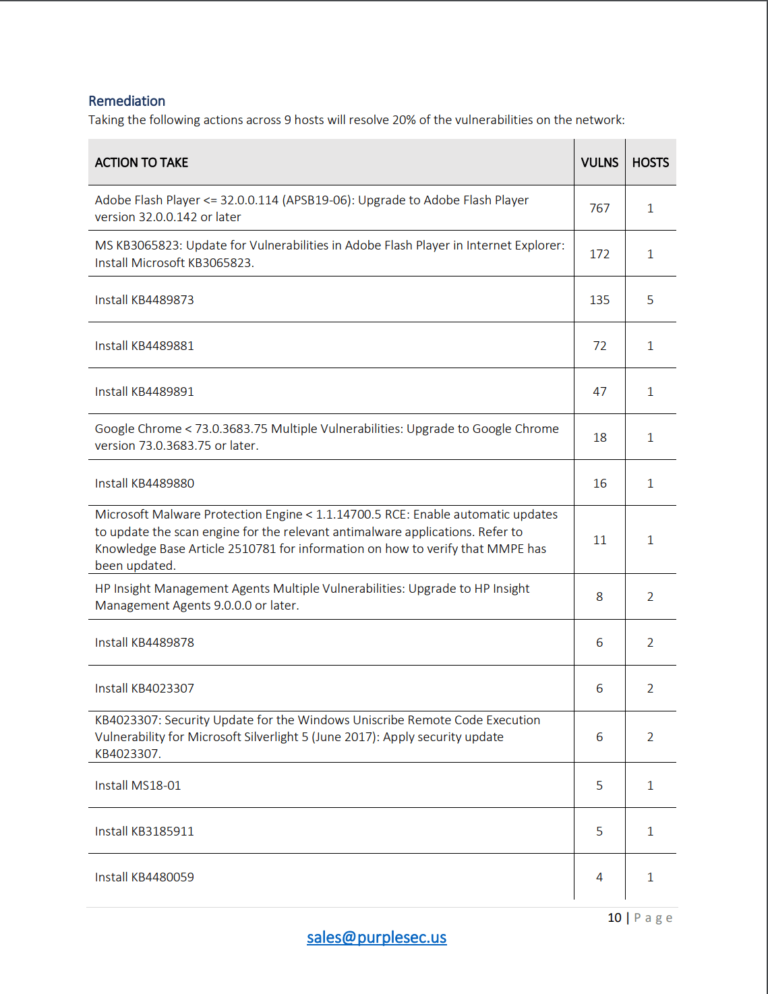
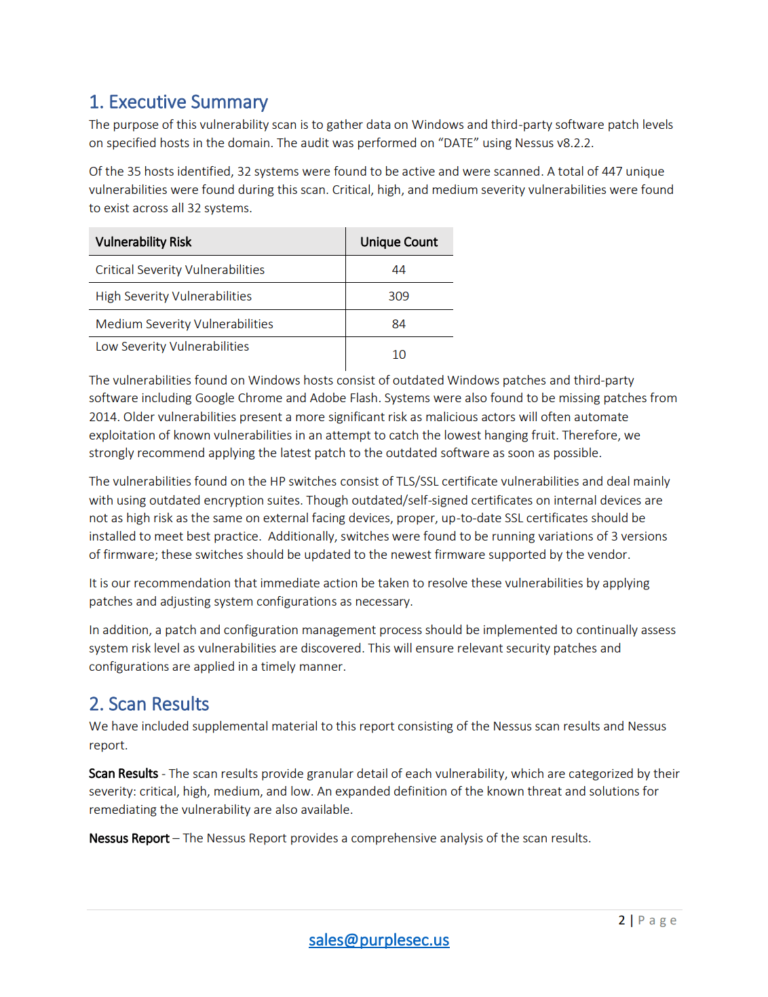
Sample Vulnerability Assessment Report
Analysis and reporting delivered by a defensive security certified professional
What’s Inside The Report?
- Threat Analysis
- Executive Summary
- Scan Results
- Risk Assessment Profile
- Remediation Planning
Vulnerability Management Best Practices
How To Centralize Your Patch Management
What Is A Vulnerability Assessment? (The Definitive Guide)
How To Improve Visibility Of Security Vulnerabilities
Our Services Work Better Together
Ready To Get Secure?
Reach Your Security Goals With Affordable Solutions Built For Small Business