You can scan a web application and website in 5 steps including:
- Setting up the scanner.
- Scanning the application for vulnerabilities.
- Having a security analyst prioritize vulnerabilities based on business risk.
- Delivering scan results and the assessment.
- Remediating and retesting vulnerabilites.
Free Security Policy Templates
Get a step ahead of your cybersecurity goals with our comprehensive templates.

What Is A Web Application Scan?
A web application scan is an in-depth examination of a web application’s security, using automated or manual techniques to identify potential vulnerabilities, flaws, and weaknesses.
Regularly conducting these scans enables developers to address and fix the discovered issues, ultimately enhancing the application’s overall security.
The goal of the scan is to identify potential security risks that could be exploited by attackers and then prioritize the issues on a severity or risk-based approach.
The scanner will search for weak passwords, outdated software versions, missing patches, misconfigured systems, and other common issues that can lead to compromise or data theft.
Learn More: Top 10 Most Exploited Security Vulnerabilities
What Does An Application Scan Look For?
Many security professionals follow the OWASP Top Ten as their guide when assessing the security posture of an application.
The scanner itself will look for common application vulnerabilities such as:
- SQL injection attacks.
- Cross-site scripting (XSS) attacks.
- Insecure cookies.
- Session management issues.
The scanner will also check for out-of-date software versions that may contain known vulnerabilities that have yet to be patched.
How Long Does The Scan Take?
The length of time required depends on the size of the system being scanned and any additional custom scans requested by the customer.
Scans typically take several hours up to a few days, depending on the complexity of the environment being scanned.
One major reason for this is due to inputs, or attack surface, of which web applications commonly have a higher volume compared to static web pages, for instance.
An increase in inputs to scan means an increase in time.
Another significant cause for why scans can take longer is the number of false positives they can generate.
In many cases, scans could produce up to 50%, 60%, or even 70% false positives, requiring the security analyst to sift through the outputs and deliver the relevant vulnerabilities for remediation.
How Often Do I Need To Scan Applications Or Websites For Vulnerabilities?
While it’s generally recommended that organizations perform regular scans every month or so depending on their risk profile, there are several factors why a web application scan should occur frequently or independent of regular cadences.
The factors that determine how often you scan your applications include:
- Compliance standards – Regular scanning for web application vulnerabilities can help organizations comply with industry regulations and standards, such as PCI DSS, HIPAA, and GDPR.
- Practicing good cyber hygiene – Scanning more often can also help maintain good cyber hygiene and a strong security posture by identifying potential security weaknesses before they can be exploited by attackers.
- Responding to emerging threats – After discovering an emerging threat, it is important to scan web applications more regularly to identify any vulnerabilities that may have been exploited. Organizations should prioritize attending to critical software that is vulnerable to attack by deploying necessary security patches and updates as soon as possible.
- Significant infrastructural changes – After significant application infrastructural changes, it’s important to scan for web application vulnerabilities. When changes are made to an application’s infrastructure, such as adding new features or updating software components, it can inadvertently introduce new vulnerabilities.
- Keeping up with business operations – As businesses evolve and grow, they introduce new web applications, features, and functionalities to support their operations. It’s important to scan regularly for web application vulnerabilities to keep up with the fast pace of business and ensure that these new additions do not introduce security weaknesses or vulnerabilities.
Why Scanning Application And Websites For Vulnerabilities Is Important
Regularly scanning applications and websites for vulnerabilities is a crucial aspect of maintaining a secure online presence, as it helps organizations defend against potential cyber-attacks and protect sensitive data.
Learn More: 9 Data Security Strategies You Need To Implement
This essential practice not only aids in identifying and addressing vulnerabilities but also enables organizations to stay current with evolving threats and security innovations.
By adopting a proactive approach, businesses can minimize downtime and financial loss while improving their overall security posture.
Some key reasons why scanning applications and websites is important include:
- Facilitating secure development and validating application updates.
- Monitoring third-party components and ensuring proper access control.
- Supporting risk management and optimizing remediation efforts.
- Assessing legacy systems and benchmarking security performance.
- Safeguarding brand reputation and enhancing user experience.
By incorporating these strategies, organizations demonstrate their commitment to cybersecurity, fostering trust with customers and partners.
This dedication not only helps maintain compliance but also contributes to an organization’s success and reputation in today’s increasingly digital world.
Steps To Scan Applications And Websites Vulnerabilities
In this section, you’ll learn the step-by-step process of setting up a web application scanner and navigating through the entire vulnerability management lifecycle, empowering you to effectively detect and address potential security risks and maintain a secure environment.
Step 1: Set Up The Scanner
To set up the scanner, you need to download software that is compatible with your operating system.
After downloading, configure the settings based on your specific needs, including the IP address ranges to be targeted during scanning intervals, potentially across multiple networks.
Authentication credentials are also required to access certain services, if necessary.
Once the settings have been configured, the scanner can be set to run scheduled scanning intervals automatically each month at predetermined times.
This can be manually triggered through command line tools provided by third-party vendors upon request.
Most organizations prefer to have scheduled automatic intervals configured ahead of time to reduce the overhead associated with manual triggering each month.
This saves valuable time and allows team members responsible for managing vulnerability scanning operations to focus their energy elsewhere throughout the organization.
This helps everyone better utilize available resources while simultaneously ensuring that all critical hosts remain safe.
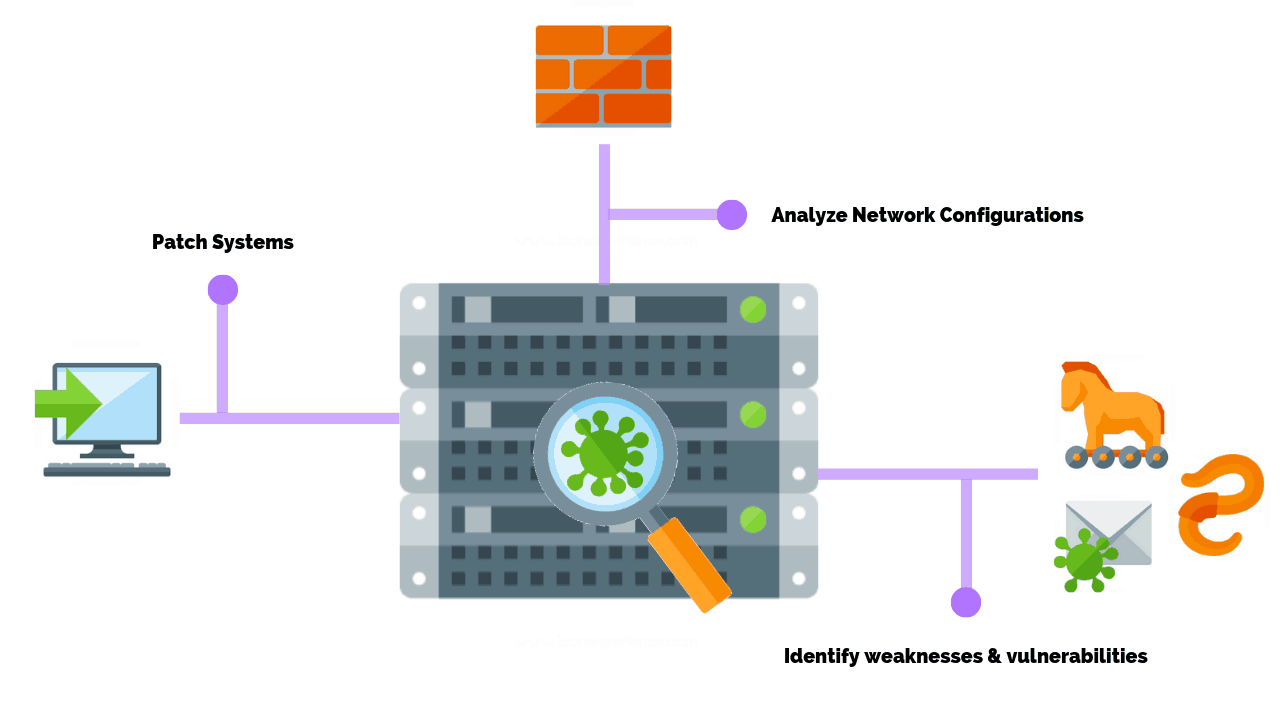
Step 2: Scan The Application For Vulnerabilities
After completing the initial setup procedures, the next step is to run the scanning interval using the predefined configurations established earlier.
This involves:
- Setting parameters for the specific target environment being scanned.
- Taking into consideration the IP address ranges assigned to the particular segment target network(s) being scanned.
- Considering any authentication credentials required to access certain services.
Once these parameters are established, the type(s) of results desired must be specified, such as whether text-based output is preferable or if HTML format is preferred.
Once all parameters are finalized, simply press “Go”, “Start”, or whatever command there may be to initiate the scanning process for automated vulnerability management.
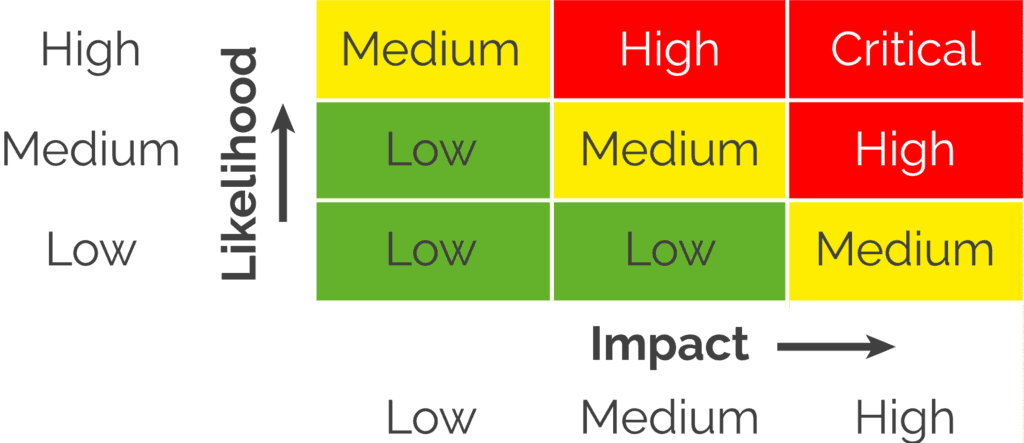
Step 3: Security Analyst Prioritizes Vulnerabilities
After the results are generated via the automated scanning interval, the final step is to review the results themselves and determine whether the findings are legitimate or false positives requiring further investigation.
The security analyst is responsible for managing the overall lifecycle security operations processes, assigning severity and risk-based levels to individual findings, and giving the highest priority to those deemed most dangerous and potentially leading to a compromise of the entire infrastructure.
Quickly responding with remediation efforts can significantly reduce risk exposure.
By doing so, the security analyst can focus their efforts on the most impactful issues first, allowing for a more efficient and effective use of resources.
Learn More: How To Conduct A Vulnerability Assessment
Step 4: Scan Results & Assessment Is Delivered
After completing the review and vulnerability assessment of individual findings, the security analyst is responsible for delivering the final report.
This report summarizes the findings, prioritizing the levels of importance and offering recommendations for addressing the issues and eliminating threats.
Once the report is delivered, it serves as the basis for a rough timeline outlining the remediation efforts needed to completely resolve the issues.
This helps ensure that everyone involved understands the seriousness of the matter and can correctly estimate the amount of resources required to complete the task successfully.
By providing a clear and concise report, the security analyst can help guide the organization’s efforts toward improving the security posture of their web applications.
Step 5: Remediation & Rescanning
After the initial remediation efforts are complete, the final step is to rerun the exact same scanning interval to verify that the issue is indeed resolved.
This helps ensure that no further effort is required to complete the job properly and provides peace of mind knowing that all identified issues have been addressed correctly.
Once the remediation efforts have been verified, confirming that everything is fixed, and rescanning helps provide further reassurance that everything has been done correctly according to plan.
The best part is that rescanning involves rerunning the same exact set of commands, which saves a lot of time and avoids unnecessary repetition of tasks that have already been performed previously.
This approach makes life easier and simplifies the entire process from start to finish.
It also provides tangible proof that the job has been done correctly, resulting in fewer stress headaches, fewer sleepless nights, and happier IT professionals.
By working smarter instead of harder and maximizing available resources, the organization can achieve a full return on investment every single time.
Web Application Scanning Tools
There are many different types of web vulnerability scanners available today but some of the most popular scanner options include:
- Acunetix
- Burp Suite Pro
- Netsparker
- OWASP ZAP
- AppSpider
Each scanner offers different features and benefits, so be sure to research them thoroughly before making a decision on which one best suits your specific needs and budget.
For example, Acunetix, Burp Suite Pro & Netsparker all focus primarily on automated scanning while OWASP ZAP & AppSpider offer both automated & manual testing capabilities.
Common Pitfalls To Overcome When Scanning Web Applications
One of the biggest challenges when it comes to scanning web applications for vulnerabilities is that many organizations don’t understand the scope of what they’re trying to protect.
It’s easy to overlook some areas in your application, such as user input fields or third-party libraries that may contain security flaws.
However, one of the major reasons for missed scope is the lack of insight and awareness into the web application’s complete attack surface.
In addition, manually testing each component is expensive and can be tedious and time-consuming.
Automating vulnerability scans can help alleviate this issue, but there is still a component that requires significant resources and expertise.
Another challenge is keeping up with changes in technology and security best practices.
For example, new versions of software may contain patches or updates that address known vulnerabilities in previous versions.
If you don’t keep your system up-to-date, you are at greater risk of attack from hackers who are actively exploiting known security flaws.
Finally, failing to plan for potential issues or risks will result in a reactive posture, forcing security teams to become overburdened and overwhelmed just trying to respond to an incident or catch up to a backlog, leading to serious consequences.
Before starting a vulnerability scan, you should create a plan that outlines what you want to accomplish and addresses any potential issues or risks upfront.
This will help ensure that your scan goes smoothly and that potential problems are addressed before they arise.
Wrapping Up
Scanning web applications and websites for vulnerabilities is a critical component of an organization’s cybersecurity strategy.
By following a structured process, such as setting up the scanner, scanning for vulnerabilities, prioritizing risks, assessing results, and performing remediation and rescanning, businesses can effectively safeguard their digital assets and maintain a secure online environment.
Regular vulnerability scanning not only enables organizations to comply with industry regulations but also helps to build trust with clients and partners.
By staying informed on the latest security challenges and employing the best practices outlined in this article, organizations can ensure that they are adequately protected against cyber threats and are well-equipped to maintain a strong security posture.
Frequently Asked Questions
How Do You Test A Website For Security Vulnerabilities?
Testing website security involves using various tools and techniques to identify and fix potential weaknesses.
Automated penetration testing, code reviews, asset inventorying, and vulnerability scanning help secure websites from cyber attacks, maintaining a robust cybersecurity infrastructure. Regular testing ensures digital asset protection.
Is It Illegal To Scan A Website For Vulnerabilities?
Determining the legality of scanning a website for vulnerabilities depends on local laws and obtaining permission from the website owner through a pen test authorization form or agreed-upon rules of engagement.
Ensure compliance with these agreements and consult a cyber security lawyer for clarity on legal implications and rights protection.
What Is The Most Commonly Reported Web Application Vulnerability?
The most frequently reported web vulnerability, as per OWASP, is injection flaws. These flaws happen when malicious data triggers unintended command execution in an interpreter.
Common examples include SQL injection and command injection. To safeguard against these attacks, implement robust input validation and be aware of the associated risks.
How Do I Check If My Website Is Infected?
To check if your website is infected, perform a comprehensive site scan using antivirus software and malware scanners. Monitor for unusual behavior, like multiple login attempts, unexpected redirects, or content changes. Regularly conduct scans to maintain security and prevent future infections.
Can I Check My Website For Vulnerabilities Online For Free?
You can use free online tools to check website vulnerabilities, but they may not cover all security issues. For comprehensive protection, combine free tools with professional ones, offering deeper scans and ensuring the site’s overall security.
Article by