The top best practices for managing vulnerabilities in the cloud include:
- Establishing KPIs
- Staying up to date with threat Intelligence feeds.
- Utilizing a vulnerability database repository.
- Leveraging automation, AI, and ML.
Free Security Policy Templates
Get a step ahead of your cybersecurity goals with our comprehensive templates.

As many organizations shift from managing their enterprise on-premise applications to the cloud, this introduces a new set of security challenges.
Depending on the cloud computing model, whether it’s hybrid, SaaS, IaaS, or PaaS, lack of visibility and access to the assets your organization manages will be difficult to support.
Without proper visibility to your systems in the cloud, your cloud environment is at high risk of exposure.
This exposure can lead to data loss, susceptibility to zero-day attacks, and can provide an easy entry point for threat actors to covertly enter your cloud environment.
In this article, we will answer why we need vulnerability management in the cloud. We will discuss how PurpleSec’s innovative solution can help effectively manage vulnerabilities and reduce the risk of exposure to your cloud environment.
Let’s begin by defining what vulnerability management is in the cloud, followed by techniques to effectively manage.
What Is Vulnerability Management In Cloud Computing?
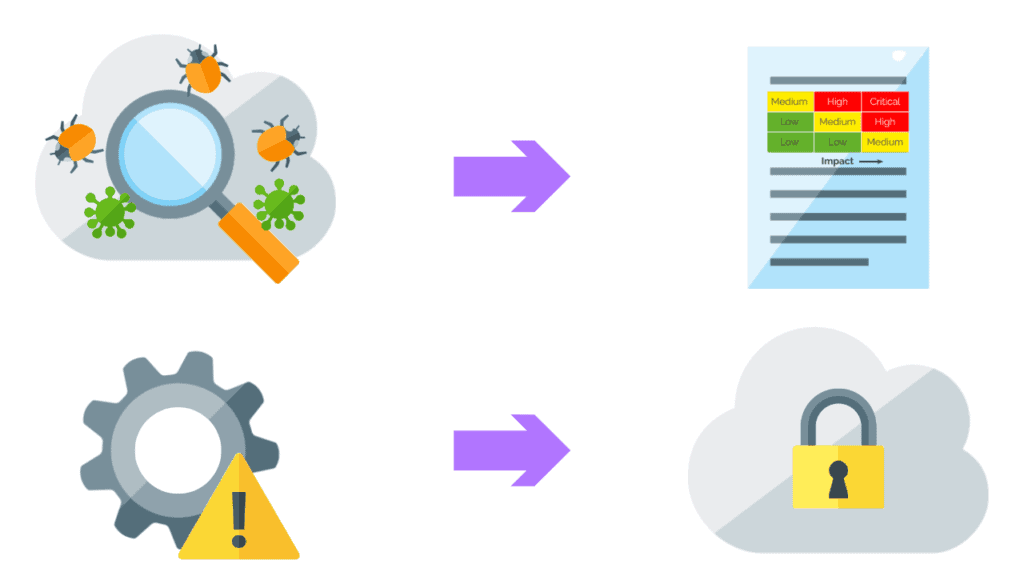
Cloud vulnerability management is a term that refers to the continuous process of identifying, reporting, and remediating security risks found within the cloud platform.
A clear understanding of vulnerability management and basic knowledge of cloud computing is critical before developing a cybersecurity strategy to effectively manage a cloud computing environment.
In this section, we will examine the terminology of cloud computing followed by the features, mitigation, and strategies commonly used for managing vulnerabilities in the cloud.
The purpose of this article is not to go into the specific details of cloud computing and every vulnerability available, but let’s start with five common cloud-based vulnerabilities many organizations face today in their cloud environments.
Best Practices For Managing Vulnerabilities In The Cloud
One of the key steps in managing vulnerabilities in the cloud is defining the key vulnerability management metrics for your environment.
In this section, we will walk through the steps to establish key metrics and how you can prepare to stay current on monitoring threats to your cloud systems.
Learn More: Cybersecurity Metrics And KPIs CISOs Use To Prove Business Value
1. Establish Key Performance Indicators (KPIs)
The first step in establishing metrics is to first define your Service Level Agreement (SLA).
SLAs are commonly used by a service provider and the customer; however, they can be used by internal teams to set baselines for their vulnerability remediation process.
Once SLAs have been established and documented within your vulnerability management policy, metrics can now be used to quantify the results of your vulnerability reports.
There are several metrics to choose from that make sense for your environment, however, a key metric for any organization measuring vulnerabilities is Mean Time to Remediate (MTTR).
This metric measures the time a vulnerability is known to the time it takes to mitigate.
Include reporting from your blue and red team tools to provide comprehensive insights into your vulnerability management lifecycle.
The outcome will result in better prioritization of remediation plans for your most critical systems through validation. This inclusive reporting approach will enable your teams to identify targets for further testing.
2. Stay Up To Date With Threat Intelligence Feeds
Ensure your vulnerability scanner utilizes more than one source for threat intelligence. Ingesting data from multiple feeds provides an opportunity for higher accuracy and the ability to perform predictive risk scoring.
3. Utilize A Vulnerability Database Repository
In addition to threat intelligence feeds, the vulnerability scanner should be integrated with a database that is linked to multiple threat resources. This extensive coverage ensures rapid analysis of vulnerabilities in your cloud environment.
4. Leverage Automation, AI, And ML
A scanning platform that incorporates automation integrated with machine learning improves the total cost of ownership.
This technology allows support teams to focus on the results, compared to spending time reviewing large amounts of historical and new vulnerabilities.
Now with an understanding of recommended best practices, let’s look at common challenges that should be addressed as you develop a strategy to manage cloud-based vulnerabilities.
Key Prerequisites Of Implementing Cloud Vulnerability Management
Creating a baseline of what you have in the cloud lays the foundation for an effective vulnerability management program.
Let’s examine the items below that you should have available before managing vulnerabilities in the cloud environment.
- Identification – Inventory and capture all assets (IP addresses, hostnames, document all inbound/outbound connections, port assignments, etc.)
- Security Risk Assessment – Independent evaluation of the cloud environment to identify misconfigurations and determine if appropriate levels of security are implemented.
- Remediation – Develop and create a strategy that documents the mitigation of identified risk per the risk assessment or via continuous vulnerability scanning.
- Vulnerability assessment report – This report provides details of the assessment and gives recommendations on the mitigation steps.
- Re-scan and VAPT certification planning – Combination of a Vulnerability Assessment and Penetration Test. This is a mandatory requirement for several industries. Although this service provides different outputs, the end goal of the test is to identify internal and external risks, followed by rescans to ensure critical vulnerabilities are addressed immediately.
Now that we’ve identified and reviewed the basic terminology and features of cloud vulnerability management, let’s identify techniques to perform the mitigation.
Challenges With Cloud Vulnerability Management
While many organizations have adopted the cloud and its many advantages, this has also presented new challenges specifically in the areas of security and data management.
Common challenges with cloud-based vulnerability management include:
- Applications created with weak security controls – Internal development teams lacking knowledge of securing a cloud application.
- Vulnerabilities in SaaS products can only be patched by the vendor.
- Selecting the right tool to manage cloud vulnerabilities and knowledge to support the platform
- Security and privacy – a through knowledge of cloud security is a requirement to ensure communication between the private and public networks is secure.
So far, we’ve discussed the features of the cloud and the challenges to managing them.
Let’s now review PurpleSec’s services that can help you meet the challenge of managing your cloud environment.
Common Cloud Vulnerabilities
- Misconfigured storage containers. Depending on the cloud vendor (AWS, Google, Oracle, or Azure), this is where your organization stores the data, i.e., database storage, backup/archives, and intellectual property. Sample vulnerability: Lack of encryption, unintended public permissions instead of private
- Poor Authentication: Primarily existing in SaaS. Basic username and passwords today are weak. Sample vulnerability: Lack of MFA (multi factor authentication).
- Insecure APIs (Application Program Interfaces): Lack of encryption or tokens used in the interfaces. Sample vulnerability: Improper use or lack of tokens used to access sensitive applications
- Poor Network configuration: Depending on the model, only necessary ports should be enabled for connectivity between your private network and the cloud systems. Sample vulnerability: Port 22 (SSH) left open by default for public accessibility.
- Improper access to critical data: Depending on the cloud vendor, the capability exists for specific credentials or ID’s to be inserted into groups linked to a specific application. Sample vulnerability: A marketing user has access to a sensitive financial application, no restrictions on what they can see.
How Do You Mitigate Cloud Vulnerabilities?
Mitigating cloud vulnerabilities reduces the risk of exposure to potential data breaches due to poor misconfiguration.
The following 10 techniques can be used to help your organization create a successful cloud mitigation strategy.
- Regularly audit the cloud service – Review permissions to applications. Monitor access between private and public resources.
- Implement an access management framework – Provides a consistent methodology for defining identities, roles, and setting up granular access permissions to your cloud applications. Can also be used with MFA technology for user authentication.
- Change all employee passwords routinely – Implement strong passwords and automatic password lifecycle.
- Fix any errors in misconfigured storage and container settings – Restrict container privileges to specific users only and review encryption settings on storage.
- Correct unrestricted port misconfigurations – Check inbound ports such as RDP and SSH from the public. Review all inbound ports, and leave nothing to default.
- Specify outbound ports to a specific address, and ensure communication is encrypted.
- Minimize and manage data leaks – Limit access to specific users or groups to storage and applications. Ensure public access is removed to any dedicated private networks.
- Back up company data, and additional servers when necessary – Backing up data to a dedicated storage area in the cloud is ideal in eliminating or reducing the impact of a ransomware attack.
- Increased employee training on cloud computing.
- Hire cyber security experts – Recommended option if expertise or your support staff is limited to implement the mitigation strategy.
Now that we have an idea of how to mitigate cloud vulnerabilities, you can now create the strategy and document the mitigation process.
Let’s now examine key areas that will help you continuously measure your remediation efforts.
Wrapping Up
In this article, we have defined what vulnerability management is in the cloud and 10 techniques you can employ to create a strategy to perform mitigation.
We also reviewed the best practices for managing vulnerabilities in the cloud and the importance of implementing metrics to measure success.
Implementing vulnerability management for the cloud requires planning and a basic understanding of cloud technology. We discussed the top challenges you should understand before you move forward with the selection of a platform to manage your cloud vulnerabilities.
With this information, you can now begin to build out a process to perform vulnerability management for your cloud environment. To help your organization reach this goal, consider the services offered by PurpleSec’s platform.
PurpleSec has a proven system that can take you through the initial risk assessment phase to the establishment of a vulnerability and patch management program.
Article by