Common Types Of Network Security Vulnerabilities
Only 14% of small businesses rate their ability to mitigate cyber risks, vulnerabilities and attacks as highly effective.
This is partly because network security vulnerabilities are constantly evolving as threat actors seek new and intuitive ways to gain access to a business’s network.
In this article, I’m going to breakdown the most common types of network vulnerabilities that threaten the security of your systems in 2022.
Before we get started, let’s define what a network vulnerability is.
Article Navigation
What Is A Network Vulnerability?
A network vulnerability is a weakness or flaw in software, hardware, or organizational processes, which when compromised by a threat, can result in a security breach.
Nonphysical network vulnerabilities typically involve software or data. For example, an operating system (OS) might be vulnerable to network attacks if it’s not updated with the latest security patches. If left unpatched a virus could infect the OS, the host that it’s located on, and potentially the entire network.
Physical network vulnerabilities involve the physical protection of an asset such as locking a server in a rack closet or securing an entry point with a turnstile.
Servers have some of the strongest physical security controls in place as they contain valuable data and trade secrets or perform a revenue-generating function like a web server hosting an eCommerce site. Often stored in off-site data centers or in secure rooms, servers should be protected with personalized access cards and biometric scanners.
Prior to investing in security controls, a vulnerability risk assessment is performed to quantify the cost and acceptable loss of the equipment and its function. As with all things in cyber security it’s a balancing act of resources vs functionality that makes for the most practical solutions.
Read More: How To Develop & Implement A Network Security Plan
What Are The Different Types Of Network Vulnerabilities?
Network vulnerabilities come in many forms but the most common types are:
- Malware, short for malicious software, such as Trojans, viruses, and worms that are installed on a user’s machine or a host server.
- Social engineering attacks that fool users into giving up personal information such as a username or password.
- Outdated or unpatched software that exposes the systems running the application and potentially the entire network.
- Misconfigured firewalls / operating systems that allow or have default policies enabled.
It’s important that your network security team address these factors when assessing the overall security posture of your systems.
When left unchecked, these vulnerabilities can lead to more advanced attacks such as a DDoS (distributed denial of services) attack, which can bring a network down to a crawl or prevent users from accessing it altogether.
1. Malware (Malicious Software)
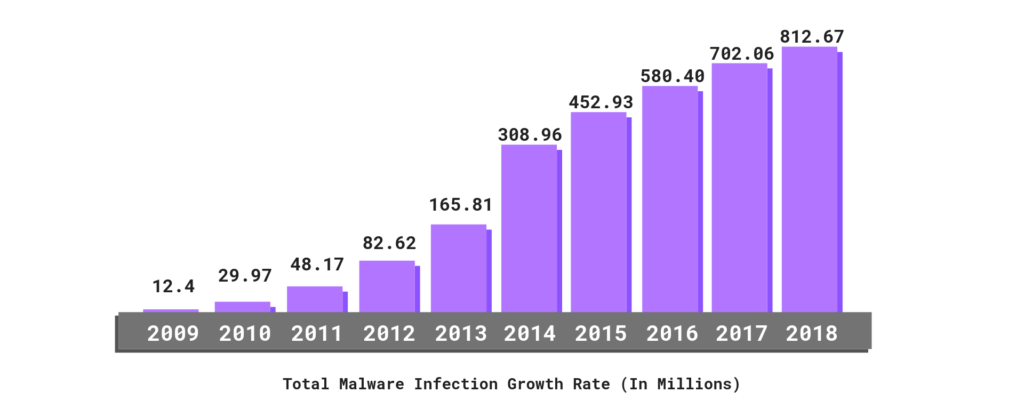
Malware is a malicious software that is unknowingly purchased, downloaded, or installed. The use of malware to exploit network vulnerabilities continue to rise hitting an all time high of 812.67 million infected devices in 2018.
 Systems infected with malware will present with symptoms such as running slower, sending emails without user action, randomly rebooting, or starting unknown processes.
Systems infected with malware will present with symptoms such as running slower, sending emails without user action, randomly rebooting, or starting unknown processes.
The most common types of malware include:
- Viruses
- Keyloggers
- Worms
- Trojans
- Ransomware
- Logic Bombs
- Bots/Botnets
- Adware & Spyware
- Rootkits
Malware is often deployed through phishing emails. In short, threat actors send emails to employees containing links to websites or embed attachments within the email itself. If an action is taken, such as clicking the link or downloading the attachment, the malicious code is executed and you can consider yourself breached.
Viruses
A virus is the most common type of malware attack. In order for a virus to infect a system it requires a user to click or copy it to media or a host. Most viruses self-replicate without the knowledge of the user. These viruses can be spread from one system to another via email, instant messaging, website downloads, removable media (USB), and network connections.
Some file types are more susceptible to virus infections – .doc/docx, .exe, .html, .xls/.xlsx, .zip. Viruses typically remain dormant until it has spread on to a network or a number of devices before delivering the payload.
Keyloggers
Keylogging, or keyboard capturing, logs a user’s keystrokes and sends data to the threat actor. Users are typically unaware that their actions are being monitored. While there are use cases for employers using keyloggers to track employee activity, they’re mostly used to steal passwords or sensitive data. Keyloggers can be a physical wire discreetly connected to a peripheral like a keyboard, or installed by a Trojan.

Worms
Similar to a virus, a worm can also self-replicate and spread full copies and segments of itself via network connections, email attachments, and instant messages. Unlike viruses, however, a worm does not require a host program in order to run, self-replicate, and propagate. Worms are commonly used against email servers, web servers, and database servers. Once infected, worms spread quickly over the internet and computer networks.
Trojan Horses
Trojan horse programs are malware that is disguised as legitimate software. A Trojan horse program will hide on your computer until it’s called upon. When activated, Trojans can allow threat actors to spy on you, steal your sensitive data, and gain backdoor access to your system.
Trojans are commonly downloaded through email attachments, website downloads, and instant messages. Social engineering tactics are typically deployed to trick users into loading and executing Trojans on their systems. Unlike computer viruses and worms, Trojans are not able to self-replicate.

Ransomware / Crypto-Malware
Ransomware is a type of malware designed to lock users out of their system or deny access to data until a ransom is paid. Crypto-Malware is a type of ransomware that encrypts user files and requires payment within a time frame and often through a digital currency like Bitcoin.
Ransomware attacks can have a devastating impact. For example, current estimates of the Baltimore ransomware attack is up to $18 million in damages. Like viruses, worms, and Trojans, ransomware is delivered via email attachments, website downloads, and instant messages and spread through phishing emails or infected websites. There is no guarantee that paying the ransom will grant access to your files/data and the recovery process can be difficult and expensive.
Logic Bombs
Logic bombs are a type of malware that will only activate when triggered, such as on a specific date/time or on the 25th logon to an account. Viruses and worms often contain logic bombs to deliver its payload (malicious code) at a pre-defined time or when another condition is met.
The damage caused by logic bombs vary from changing bytes of data to making hard drives unreadable. Antivirus software can detect the most common types of logic bombs when they’re executed. However, until they do, logic bombs can lie dormant on a system for weeks, months, or years.
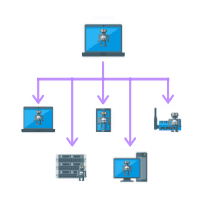
Bots/Botnets
Botnet, short for roBOT NETwork, is a group of bots, which are any type of computer system attached to a network whose security has been compromised. They are typically controlled remotely.
The Mirai botnet was able to gain control of internet of things (IoT) connected devices like your DVR, home printer as well as smart appliances by entering the default username and password that the devices shipped with. The threat actors deployed a DDoS (distributed denial of service) attack by sending large amounts of data at a website hosting company, causing many popular websites to be taken offline.

Adware & Spyware
Adware and Spyware are both unwanted software. Adware is designed to serve advertisements on screens within a web browser. It’s usually quietly installed in the background when downloading a program without your knowledge or permission. While harmless, adware can be annoying for the user.
Spyware, on the other hand, is a type of malware designed to gain access and damage your computer. Spyware collects user’s information such as habits, browsing history, and personal identification information (PII). Attackers then sell your data to advertisers or data firms, capture your bank account information, or steal your personal identity. Spyware is often downloaded in a software bundle or from file-sharing-sites.

Rootkits
Rootkits are a back door program that allows a threat actor to maintain command and control over a computer without the user knowing. This access can potentially result in full control over the targeted system. The controller can then log files, spy on the owner’s usage, execute files and change system configurations remotely.
While traditionally deployed using Trojan horse attacks, it’s becoming more common in trusted applications. Some antivirus software can detect rootkits, however, they are difficult to clean from a system. In most cases, it’s best to remove the rootkit and rebuild the compromised system.
2. Social Engineering Attacks
Social engineering attacks have become a popular method used by threat actors to easily bypass authentication and authorization security protocols and gain access to a network.
 These attacks have increased significantly in the last 5 years becoming a lucrative business for hackers. Internal users pose the greatest security risk to an organization typically because they’re uneducated or unaware of the threat. Accidentally downloading an attachment or clicking a link to a website with malicious code can cost thousands in damages.
These attacks have increased significantly in the last 5 years becoming a lucrative business for hackers. Internal users pose the greatest security risk to an organization typically because they’re uneducated or unaware of the threat. Accidentally downloading an attachment or clicking a link to a website with malicious code can cost thousands in damages.
Note: This does not prove malicious intent. The user could be a victim of a social engineering attack.
The most common types of social engineering attacks include:
- Phishing emails
- Spear phishing
- Whaling
- Vishing
- Smishing
- Spam
- Pharming
- Tailgating
- Shoulder surfing
- Dumpster diving
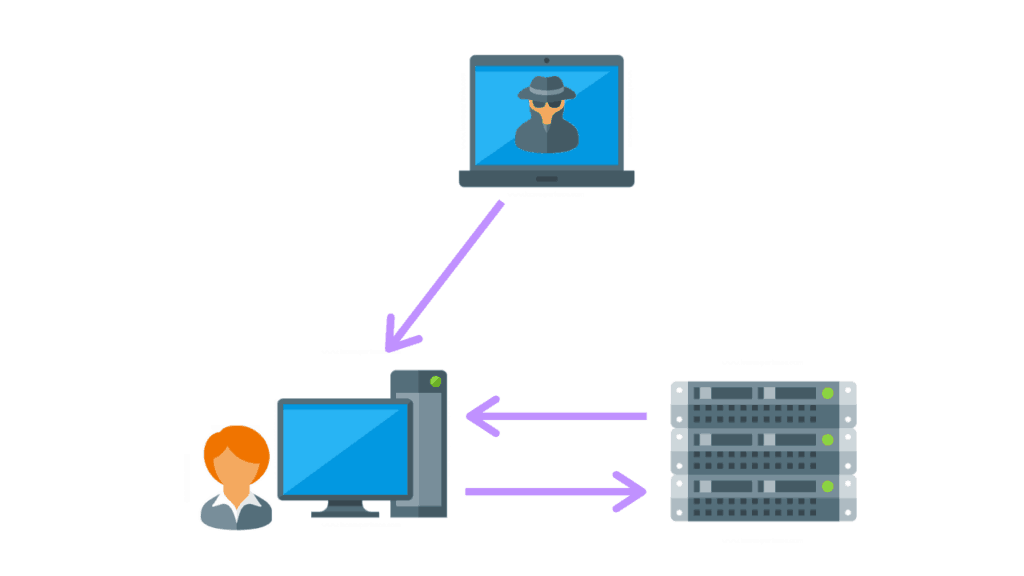
Phishing Email
A phishing email scam is an online threat that appears to be from a legitimate user or business. These scams attempt to trick users into providing sensitive information such as a username and password, downloading or opening an application, or transferring money. Phishing relies on creating false trust, which is why threat actors will often send emails from familiar websites.
 When the user enters their credentials the bad guys log the username and password. The damage from a phishing attack can vary based on what information they have access to. For instance, a personal user may have their bank account siphoned or their identity stole. For a business, an attacker with access to an internal user’s computer can attempt to escalate their privileges and lock out system administrators.
When the user enters their credentials the bad guys log the username and password. The damage from a phishing attack can vary based on what information they have access to. For instance, a personal user may have their bank account siphoned or their identity stole. For a business, an attacker with access to an internal user’s computer can attempt to escalate their privileges and lock out system administrators.
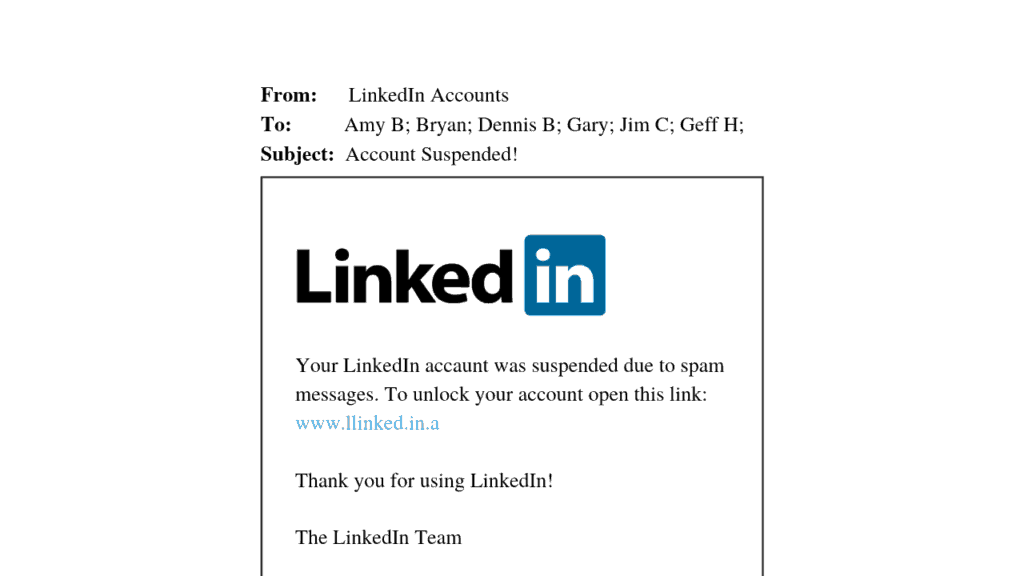
Spear Phishing
Spear phishing is similar to phishing in that it attempts to trick a user. However, spear phishing attacks are designed to use personal information to get you to click a link. They will also sometimes use urgency or a risk of monetary value to bait their victims.
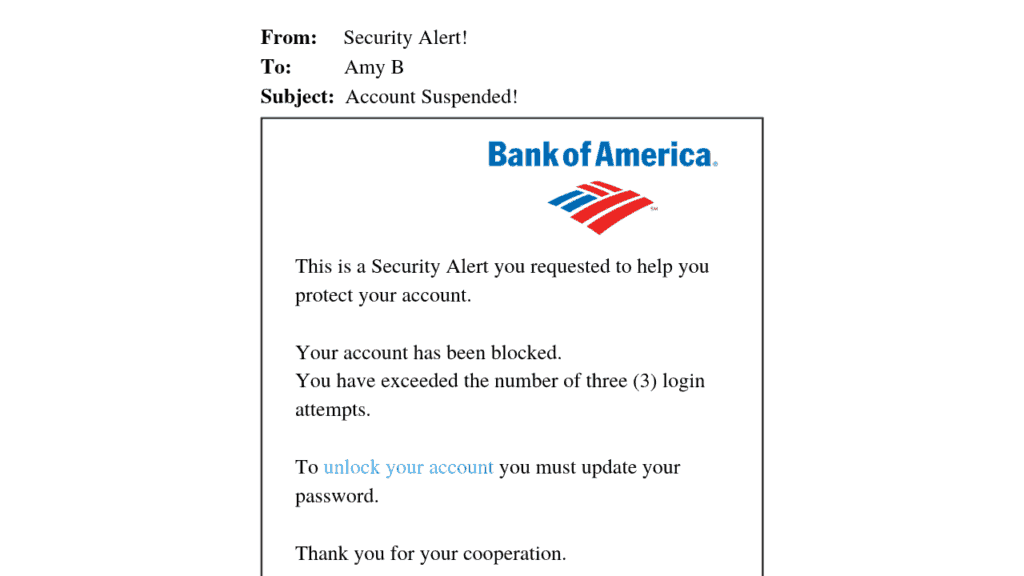
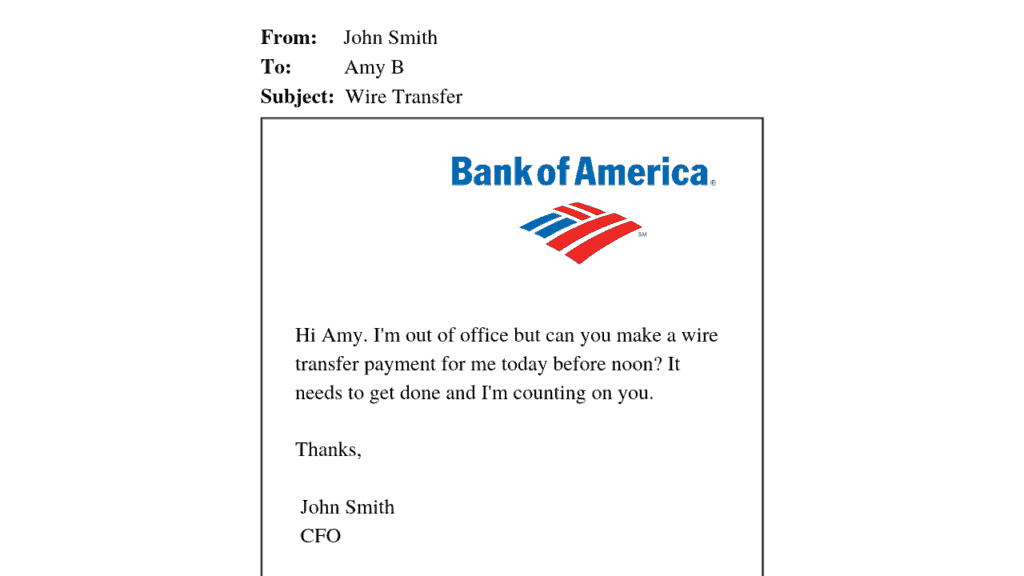
For example, the email from Bank of America to Amy B shows that someone has attempted to access her account and that the bank has locked it. In order for Amy to resolve the issue all she has to do is click on the link to reset her password. The threat actors are hoping Amy will be panicked about her money, clicks the link, and then gives them her login information.
Whaling
Whaling is a type of phishing attack that targets a high-profile business executive or manager with more critical information to lose. Whaling emails are different from other phishing attacks in that the emails and web pages serving the scam appear to be official.
Threat actors can easily use information from executives with information posted on the company’s website or social media to craft a unique message.
Vishing
Vishing, the combination of voice and phishing, is a phishing attack that takes place over the phone, typically a VoIP (Voice over IP) line. Threat actors are able to use tools specific to VoIP systems, thereby hacking their auto dialers to send robo messages from a spoofed VoIP address.
In 2018, nearly 48 billion robocalls were made in the U.S., an increase of 57% over 30 billion in 2017, making vishing one of the fastest growing social engineering attack. In some cases, threat actors will attempt to confuse you by saying that your system is hacked and the password needs to be updated. Or that they need to request an urgent payment because they have some discrediting “information” on you. Sometimes, the threat actors will get clever by pretending to be friendly.
They may even ask questions like:
- What’s your dog’s name?
- What street did you grow up on?
- What was the color of your first car?
Smishing
 Smishing is a cyber attack that uses SMS text messages to mislead its victims into providing sensitive information to a threat actor.
Smishing is a cyber attack that uses SMS text messages to mislead its victims into providing sensitive information to a threat actor.
Sensitive information includes your account name and password, banking account or credit card numbers. The threat actor may also embed a short url link into the text message, inviting the user to click on the link which in most cases is a redirect to a malicious site.
Spam
Spam has been plaguing our inbox since the inception of email communication. Spam is an attempt to send mass emails to a large number of users. The emails are sometimes annoying solicitations or they can be scams or hoaxes.
You’re likely familiar with the popular Nigerian prince scam that’s responsible for millions of dollars in damages. In more recent history, spam has been the primary delivery system for phishing emails carrying malware in email attachments and in hidden messages in images.

Pharming
Pharming is a type of social engineering attack that misdirects a user’s website’s traffic to a fake site. Similar to phishing, pharming occurs when code is installed on the computer that modifies the destination URL to the attacker’s. Pharming attacks typically take place by changing the hosts file on the computer or by exploiting a vulnerability in the DNS server software. Pharming can result in the loss of data, credit card information, or lead to identity loss.
Tailgating
Not all social engineering attacks are done remotely or with the use of an electronic device. Tailgating is a simpler type of social engineering attack where the threat actor gains physical access to a facility by following a user through a security check point. Common courtesy is often how the threat actors break in.
Holding a door for the person behind you, joining a crowd of people, and fooling authorized users into letting them in are all methods used. Businesses must have strict access control rules to prevent unauthorized individuals as well as employee training to quickly respond and report suspicious activity.

Shoulder Surfing
Shoulder surfing is a type of social engineering that refers to obtaining personal or private information through direct observation. It’s very easy for a threat actor to casually glance over the shoulder of employee to view their monitor.
Users should always be aware of their surroundings when using login names and passwords or when accessing sensitive data. This is especially true when using a computer, smartphone or ATM in a crowded area.

Dumpster Diving
Dumpster diving is social engineering reconnaissance. The threat actors are looking for any piece of information or clues they can get their hands on. They’re looking for account numbers, special events, contact names, numbers and more.
This information is then used in spear phishing and whaling attacks where personal identification information (PII) is used against the victim in an attempt to fool them. Dumpster diving is typically legal since trash does not have an owner, however, not all states abide to this law. It is also illegal to trespass on to someone’s property to then rummage through their trash.
3. Outdated Or Unpatched Software
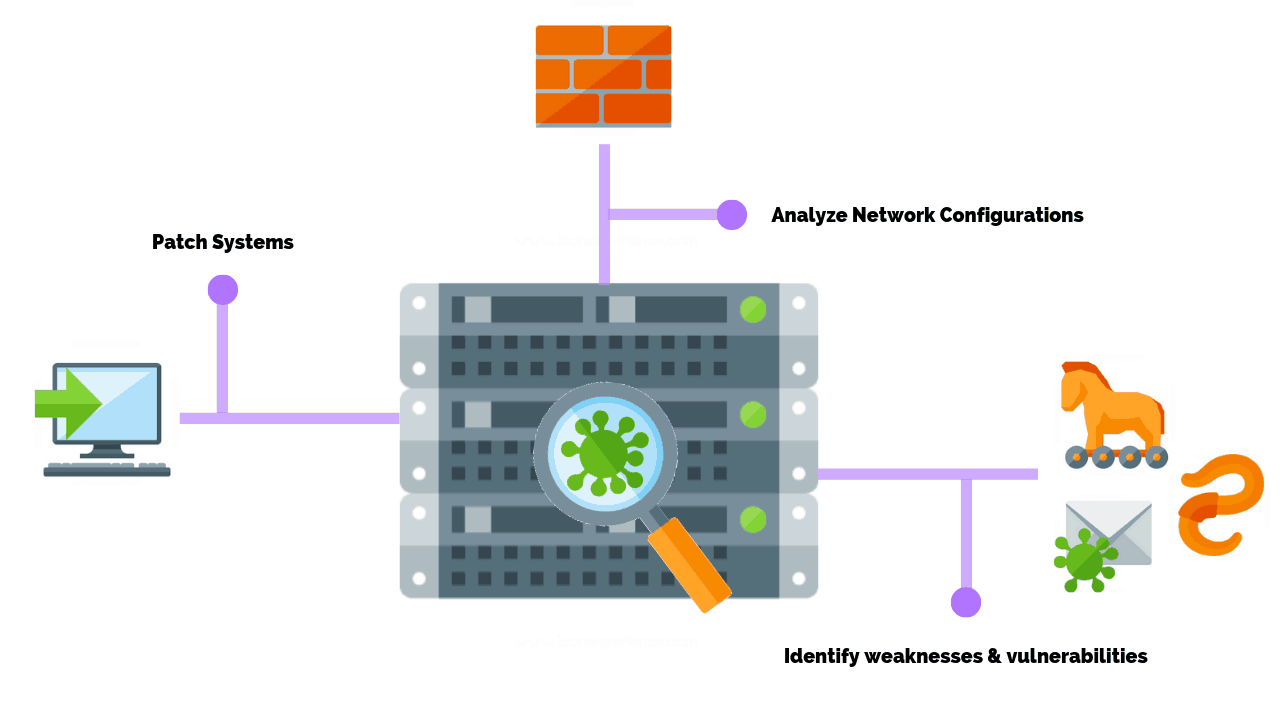
Software developers are constantly coming out with new patches to fix bugs and errors to reduce vulnerabilities. Some applications are millions of lines of code long making vulnerabilities an inevitable part of software deployment. As a result, developers deploy patches to software to remediate these vulnerabilities, although patches may also be performance or feature upgrades.
Maintaining the security of software code is an on going battle, with major companies like Facebook, Apple, and Microsoft releasing patches daily to defend against new cyber threats. It’s not uncommon for software and hardware vendors to announce end of life dates (EOL). These legacy products are often no longer profitable and cost resources (software developers) to support.
As an example, Microsoft announced that the Windows 7 operating system will no longer be supported after January 14, 2020.
Systems running Windows 7 after January 14th will pose a serious security risk to a company’s network. It’s recommended that these systems be updated to a current operating system, like Windows 10. Performing routine vulnerability scans and vulnerability assessments are one way to identify and remediate known vulnerabilities on your network.
4. Misconfigured Firewalls
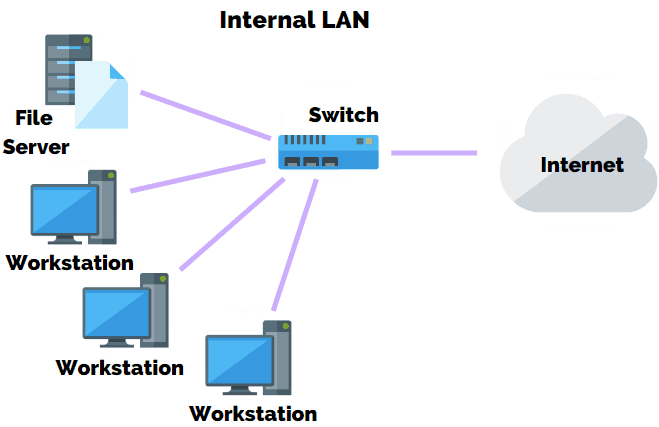
One of the most significant threats to an organization is exposing your internal network or servers to the internet. When exposed, threat actors are easily able to spy on your traffic, steal data, or compromise your network.
What Does A Firewall Do?
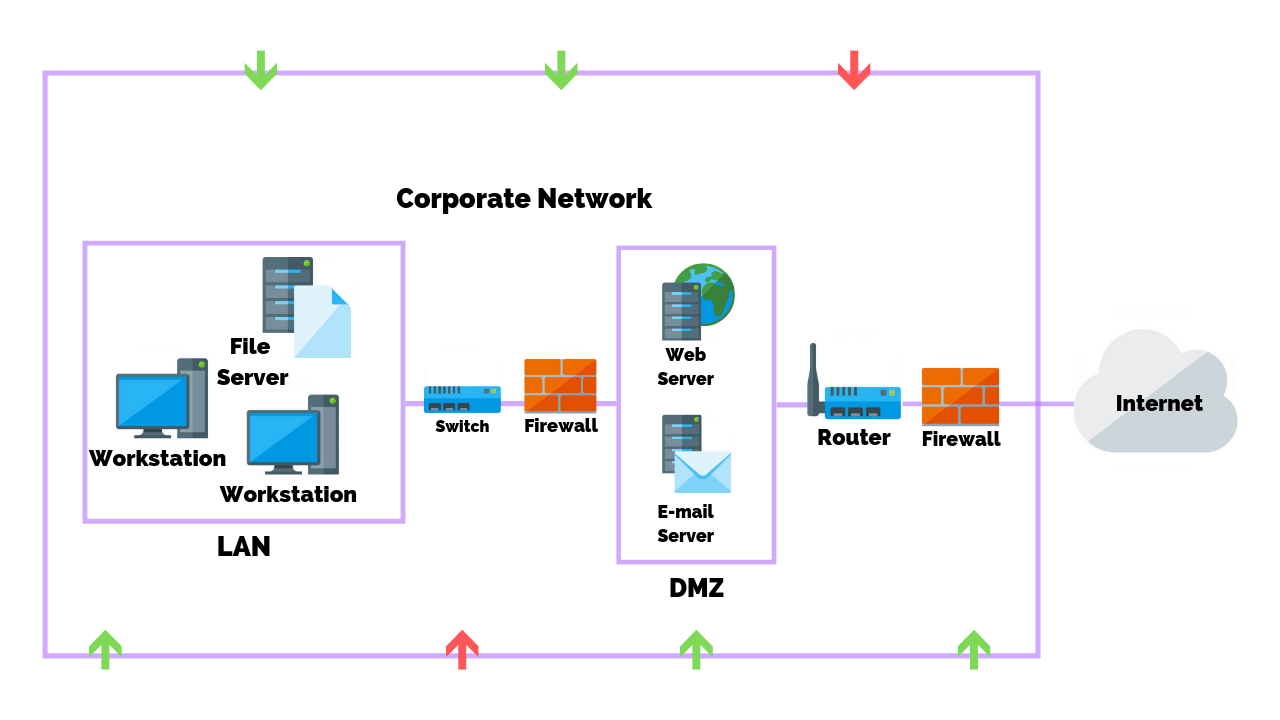
Firewalls are often deployed in the DMZ (demilitarized zone) which serves as a buffer between the internet and your internal network. Firewalls are the front line of defense, monitoring inbound and outbound traffic and choosing whether to allow or block traffic based on a set of rules.
Network administrators create rules for incoming and outgoing network communication. For example, website traffic is sent through HTTP (hypter text transmission protocol) or HTTPS (hypter text transmission protocol secure).
A firewall is sometimes set up in front of a web server and configured to allow traffic from port 80 (HTTP) and port 443 (HTTPS) to the web server. Firewalls that are protecting internal networks may then be configured to block those ports from sending or receiving traffic.
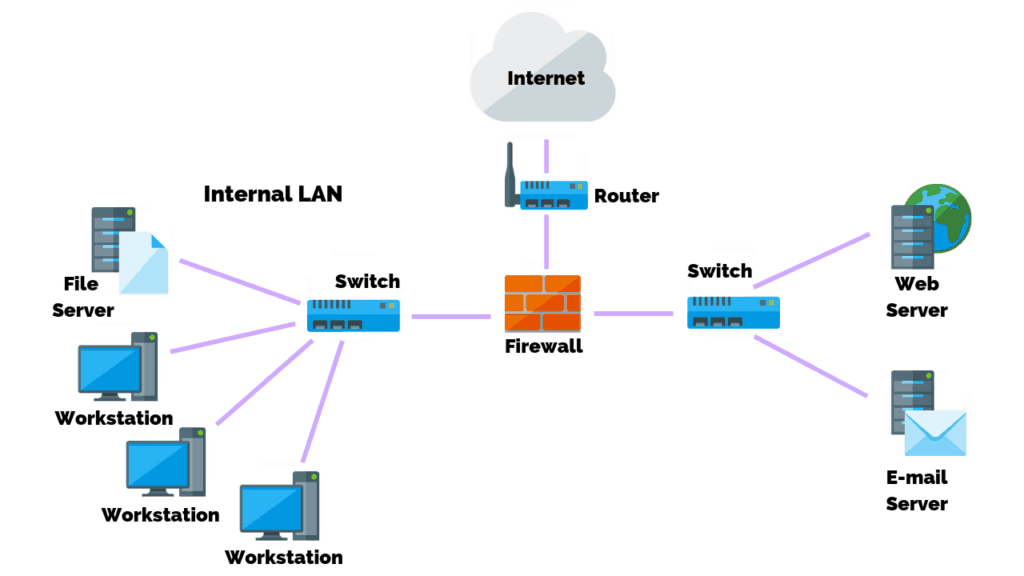
However, not all traffic should be allowed into a network. For example, Internet Control Message Protocol (ICMP) is used to test basic connectivity of devices in a network. This traffic is often blocked on a firewall and router as threat actors can send a ping request, which can check the connectivity between two systems to discover devices on a network.
If the firewall isn’t configured correctly to block this traffic then threat actors can monitor traffic or deploy an attack on your network. Finally, firewall penetration tests are performed to test the effectiveness of your security controls.
5. Default Security Features
Many systems today run on the Microsoft operating system (OS), however, Linux and Apple make up the three main operating systems used. In the case of Microsoft, their system ships with the default security settings enabled.
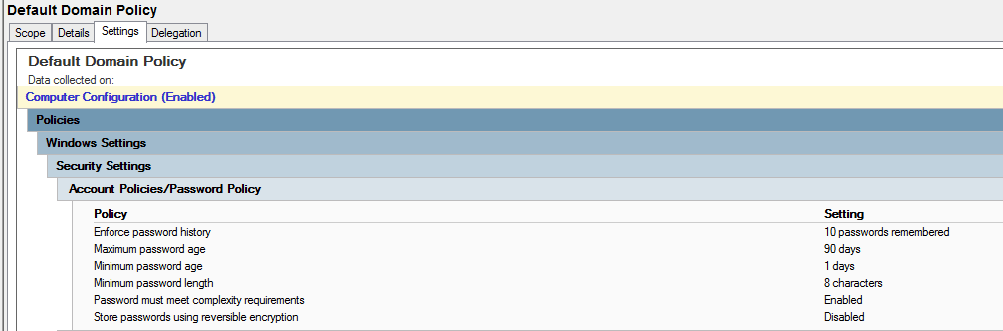
The example above is a business’s default domain password policy.
- Enforce password history stores the number of previous passwords used. The longer a password is used the more susceptible it is to being compromised.
- Maximum password age determines how long the password remains in use before it expires. Experience tells us that users will not change their password unless they are forced to do so.
- Minimum password age determines the period of time (in days) that a password can be used before the system requires the user to change it.
- Minimum password length is self explanatory. The longer the password the more difficult it is to crack.
- Password complexity requirements include use of special characters (!$&), numbers (123), and a mixture of upper case and lower case letters.
- Store passwords using reversible encryption means encrypting and storing passwords as well as being able to decrypt them.
While the default settings are good security precautions to take they can be greatly improved upon.
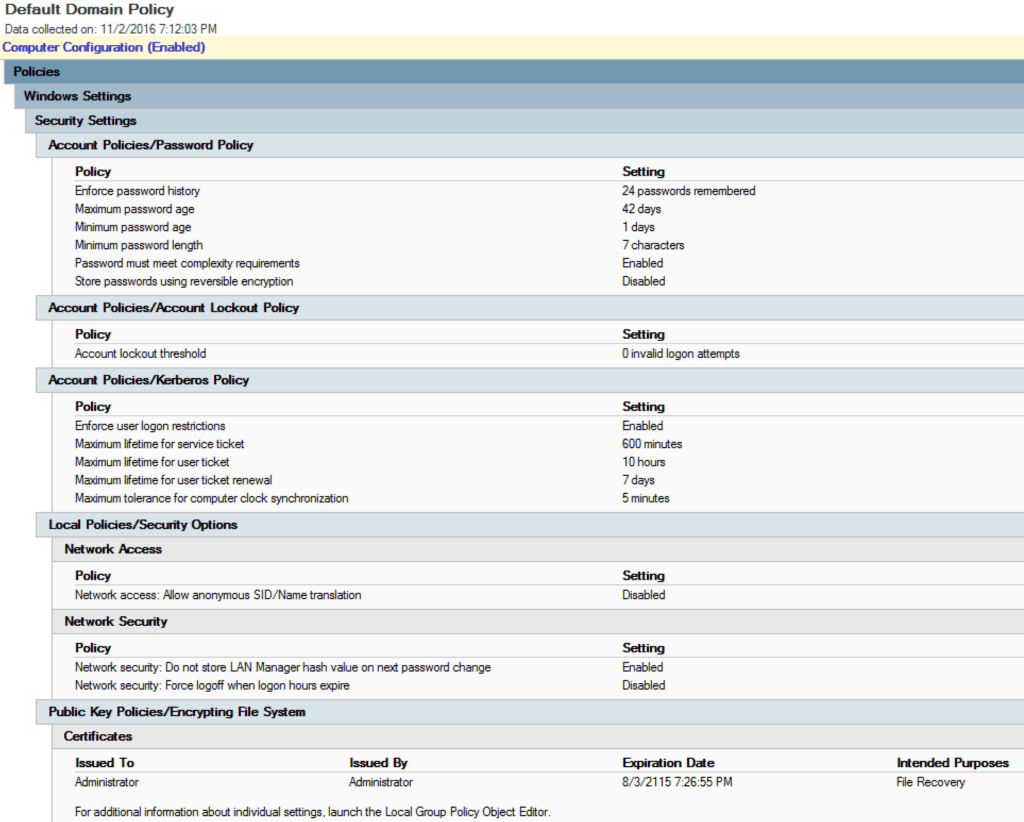
In this example, Microsoft recommends changing the password history from 10 to 24 passwords and reducing the maximum password age from 90 days to 42 days. It’s ultimately the responsibility of the network administrator to ensure that the domain, workstations, and devices are set up to adhere to cyber security policies within the organization.
Conclusion
Network vulnerabilities are always at threat of being compromised as malicious actors search to exploit and gain access into your business’s system. Malware and social engineering attacks are the single greatest threat to an organization and its users. Outdated software often contain vulnerabilities that are not present in the current version and pose a security risk. Finally, misconfigured firewalls and default policy settings on operating systems are at serious risk of exposure to a threat actor.
Related Articles
- Internal VS External Vulnerability Scans; What’s The Main Difference?
- The Ultimate List Of Cyber Security Statistics For 2019
- 50 Free Cyber Security Policy Templates To Secure Your Network
- How To Perform A Successful Network Vulnerability Assessment
- What Is A Red Team VS A Blue Team In Cyber Security?



Sam
I helped a Church with their computers and the present person doing so, thinks that avast will protect all the computers on the system with no help from the users running weekly or monthly avast programs. I worry because their books and banking are on one of the computers on the network and the present IT thinks it is separate from the rest; is this possible?
Jason Firch, MBA
Hi Sam! Anti-malware programs like Avast can be configured for auto-updates and should be configured to scan on a specific schedule. However, someone should be confirming that these scans are being completed. Books and banking should be isolated from the rest of the network meaning a separate VLAN or separate network entirely. You can confirm this by testing connectivity from other clients to that computer. If they can communicate then it’s not isolated.