Previous
Dropbox Suffers Data Breach Following Phishing Attack
Learn how PurpleSec’s experts can protect your business against the latest cyber attacks.
Author: Dalibor Gašić / Last Updated: 12/04/2022
Reviewed By: Michael Swanagan, CISSP, CISA, CISM
View Our: Editorial Process
Table Of Contents
Summary Of The Attack
- On November 1 of this year, Dropbox confirmed that it had experienced a data breach
- An unknown attacker gained access to credentials, data, and other secrets within their private GitHub code repositories.
- Dropbox did disclose that certain plain text secrets, such as API keys and other credentials, were included in the code.
- A “few thousand names and email addresses belonging to Dropbox employees were also exposed.
What Happened?
On November 1 of this year, Dropbox confirmed that it had experienced a data breach and that an unknown attacker gained access to credentials, data and other secrets within their private GitHub code repositories.
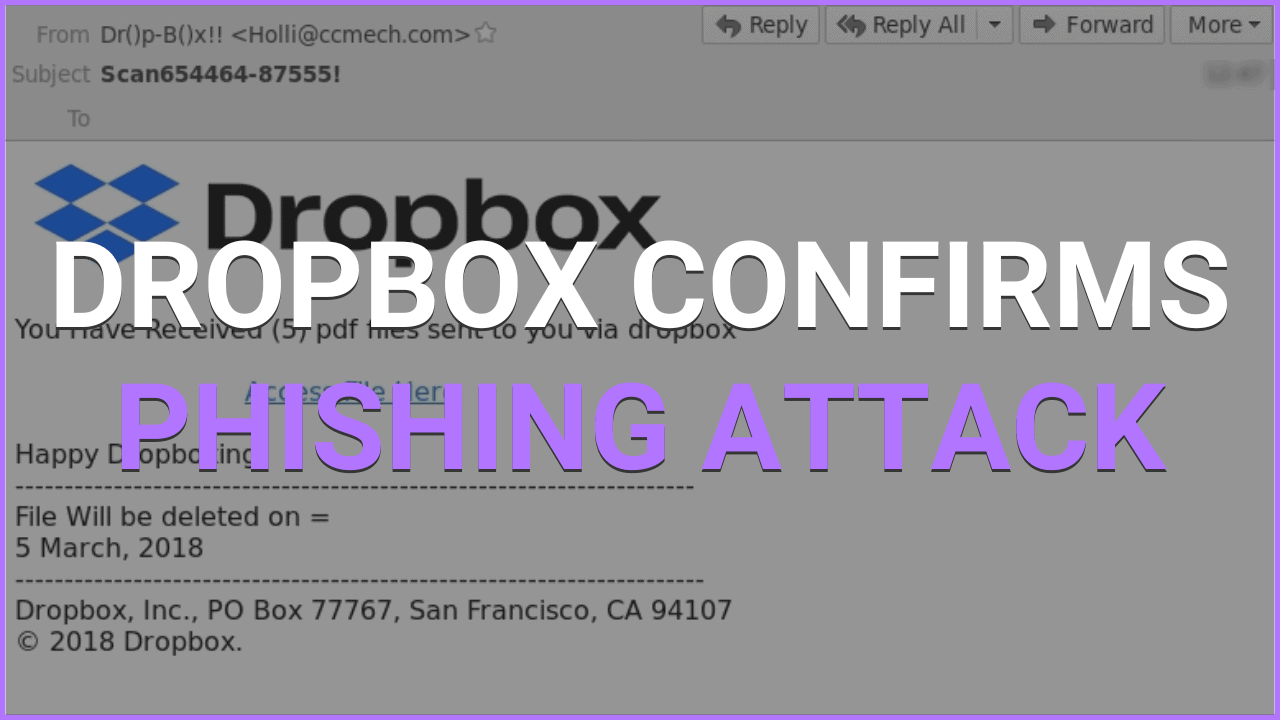
A threat actor gained access to a Dropbox developer’s GitHub account after he fell victim to a phishing attack.
This hacked developer gave the attacker access to around 130 internal code repositories.
Dropbox maintains that these code repositories were not linked to its core programs, but instead included modified third-party libraries, internal prototypes, and other internal tools.
While the repos may not be linked to its main programs, Dropbox did disclose that certain plain text secrets, such as API keys and other credentials, were included in the code, as well as a “few thousand names and email addresses belonging to Dropbox workers.”
Anatomy Of The Attack
- The attacker sent out a mass phishing email impersonating CircleCI, a major CI/CD software utilized by Dropbox internally.
- The phishing email sent the victim to a bogus CircleCI login page, where they submitted their GitHub credentials. CircleCi enabled users to log in using their GitHub credentials.
- Users were also asked to provide a One-Time Password (OTP) generated by their hardware authentication key,
- The attacker would get access to the victim’s GitHub account using the OTP and credentials given by the user
- The attacker copied 130 internal repositories, which contained both public and confidential code.
- The attacker’s future moves are unclear at this time, however, in prior assaults, the attacker looked for sensitive information such as secrets in order to migrate laterally into more sensitive systems.
Github User’s Are Prime Targets Of Phishing Attacks
Few people are aware that Github disclosed in September that many users were being targeted by phishing attackers imitating CircleCI. The hackers then obtained their user credentials as well as their two-factor authentication codes.
Dropbox’s Response
“We think the risk to clients is negligible,” Dropbox’s security team stated in a statement, which disclosed the breach.
“We have alerted people affected and are revealing more here because we take our commitment to security, privacy, and openness seriously,” and they have also claimed that “We also investigated our logs, and found no indication of successful misuse.”
This would imply a low danger to Dropbox users, but as we’ve seen in many prior breaches, attackers may move laterally from internal tools into core infrastructure; however, there is presently no evidence to corroborate this.
Dropbox did, however, reveal that “the code and data around it also included a few thousand names and email addresses belonging to Dropbox employees, present and previous customers, sales prospects, and vendors.”
I’m A Dropbox User, What Can I Do?
We would not consider this breach to be a reason to stop using Dropbox.
Now is an excellent moment to consider and implement standard security measures, such as routinely changing passwords and enabling MFA on your storage account.
Also, as usual, keep an eye out for any questionable emails or unexpected URLs that arrive in your inbox.
Related Articles:

Dalibor Gašić
Dalibor is a Senior Security Engineer with experience in penetration testing having recently served over 8 years in the Ministry of Internal Affairs in the Department of Cyber Security in Serbia.
Recent Attacks
- Top 10 Cyber Attacks In 2022
- Top 10 Vulnerabilities In 2022
- Rackspace Ransomware Attack
- Dropbox Suffers Data Breach
- Iranian APT Uses Log4j
- Google SEO Poisoning Campaign
- Killnet DDoS Target Airports
- Advocate Aurora Health Data Leak
- Microsoft 2.4 TB Data Leak
- Optus Exposes 2.1M Customers
- $570M Binance Coin Hack
- TikTok Denies Cyber Attack
- NATO Data Leak
- Uber’s Systems Compromised
- Cisco Cyber Attack
- Samsung Exposes PII
Popular Articles




 HEALTHCARE
HEALTHCARE GOVERNMENT
GOVERNMENT CRYPTO
CRYPTO